...
Note: EALTEdge Blueprint Deployment has been tested on Cloud VM and is not tested on Bare-Metal Environment. Though, theoretically deployment should work in bare metal, provided hardware and software prerequisites are met. Kindly refer R5 R6 - Test Documentation of Enterprise Applications on Lightweight 5G Telco Edge (EALTEdge) to get details on the tested deployment.
...
2. Setup password-less login from ocd to center and ocd to edge.
...
-
- If you get authentication issue you can change the permission
# Open file: vi /etc/ssh/sshd_config
...
- sudo systemctl restart ssh.service # sshpass
For EdgeGallery AIO mode:
Login from ocd to center and ocd to edge in a single node.
- sshpass -p <password> ssh-copy-id -p <ssh-port> -o StrictHostKeyChecking=no root@<node_
...
- ip>
For EdgeGallery Muno mode:
Login from ocd to center in a controller node
- sshpass -p <password> ssh-copy-id -p <ssh-port> -o StrictHostKeyChecking=no root@<controller-node_ip>
- sshpass -p <password> ssh-copy-id -p <ssh-port> -o StrictHostKeyChecking=no root@<edge-node_ip>
Login from ocd to edge in a edge node
- sshpass -p <password> ssh-copy-id -p <ssh-port> -o StrictHostKeyChecking=no root@<controller-node_ip>
- sshpass -p <password> ssh-copy-id -p <ssh-port> -o StrictHostKeyChecking=no root@<edge-node_ip>
3. These command are require in both AIO and MUNO(Controller and Edge Node ) mode.
cp -p /etc/passwd /etc/passwd.bkp
cp -p /etc/group /etc/group.bkp
id ubuntu
groupmod -g 600 ubuntu
id ubuntu
4. Review and Change Parameters
For EdgeGallery AIO Mode:
...
3. These command are require in both AIO and MUNO(Controller and Edge Node ) mode.
cp -p /etc/passwd /etc/passwd.bkp
cp -p /etc/group /etc/group.bkp
id ubuntu
groupmod -g 600 ubuntu
id ubuntu
4. Review and Change Parameters
For EdgeGallery AIO Mode:
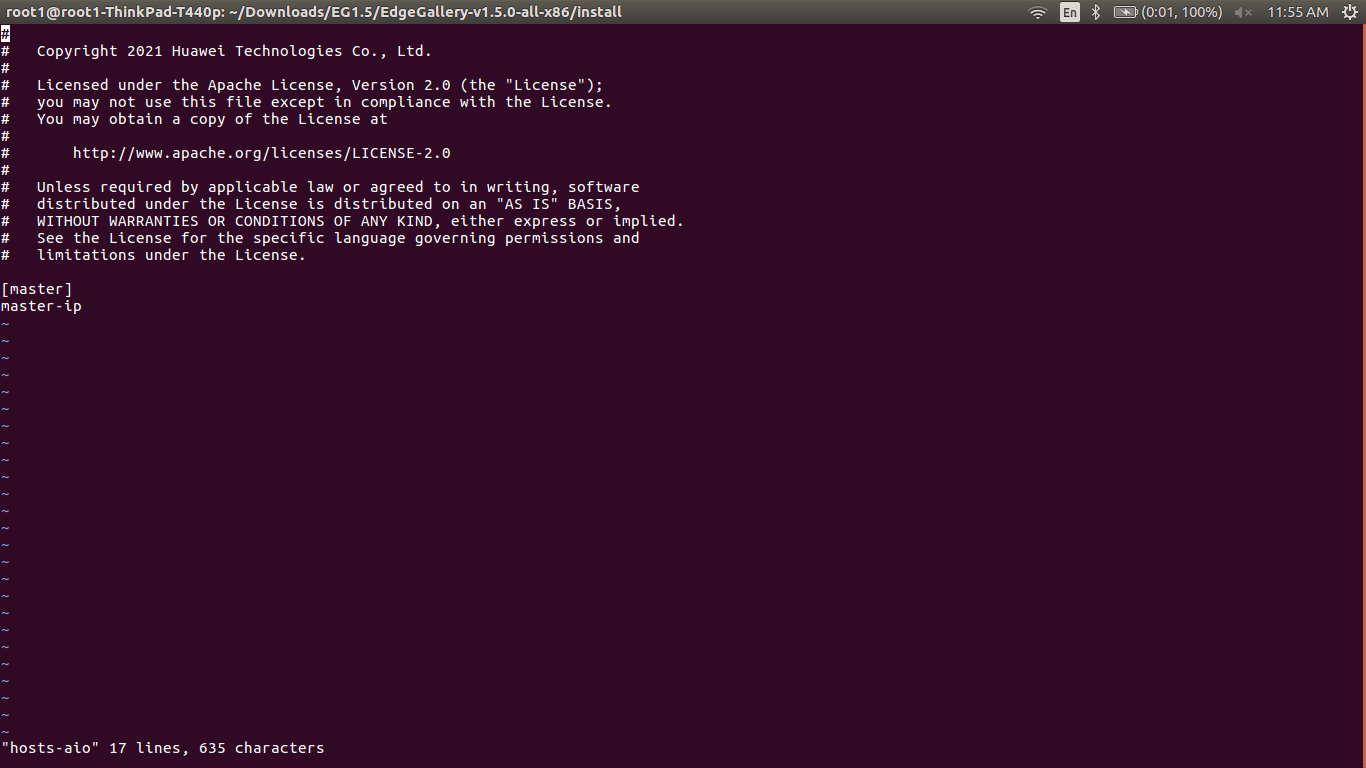
ealt-edge/ocd/infra/playbooks/hosts-aio
- Here user can use the private IP as a master IP
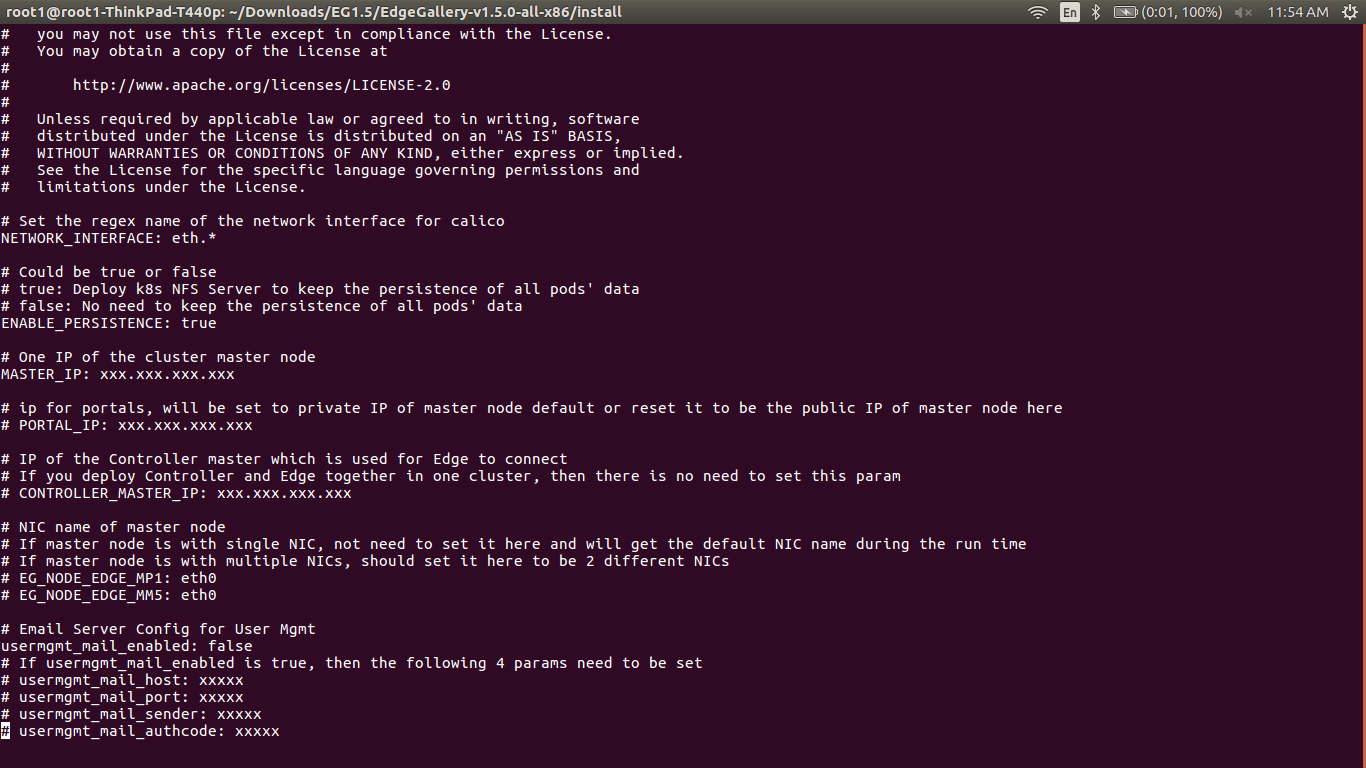
ealt-edge/ocd/infra/playbooks/var.yml
- NETWORK_INTERFACE: regex for network interface on the VM. (user can be check ineterrface name by ifconfig and provide inerface name accordingly for example like eth.* )
- MASTER_IP: Here user can use the private IP as a MASTER_IP
- PORTAL_IP: If portal need to be access over internet then uncomment the PORTAL_IP and use public IP as a PORTAL_IP otherwise portal will be accessible only on private IP default.
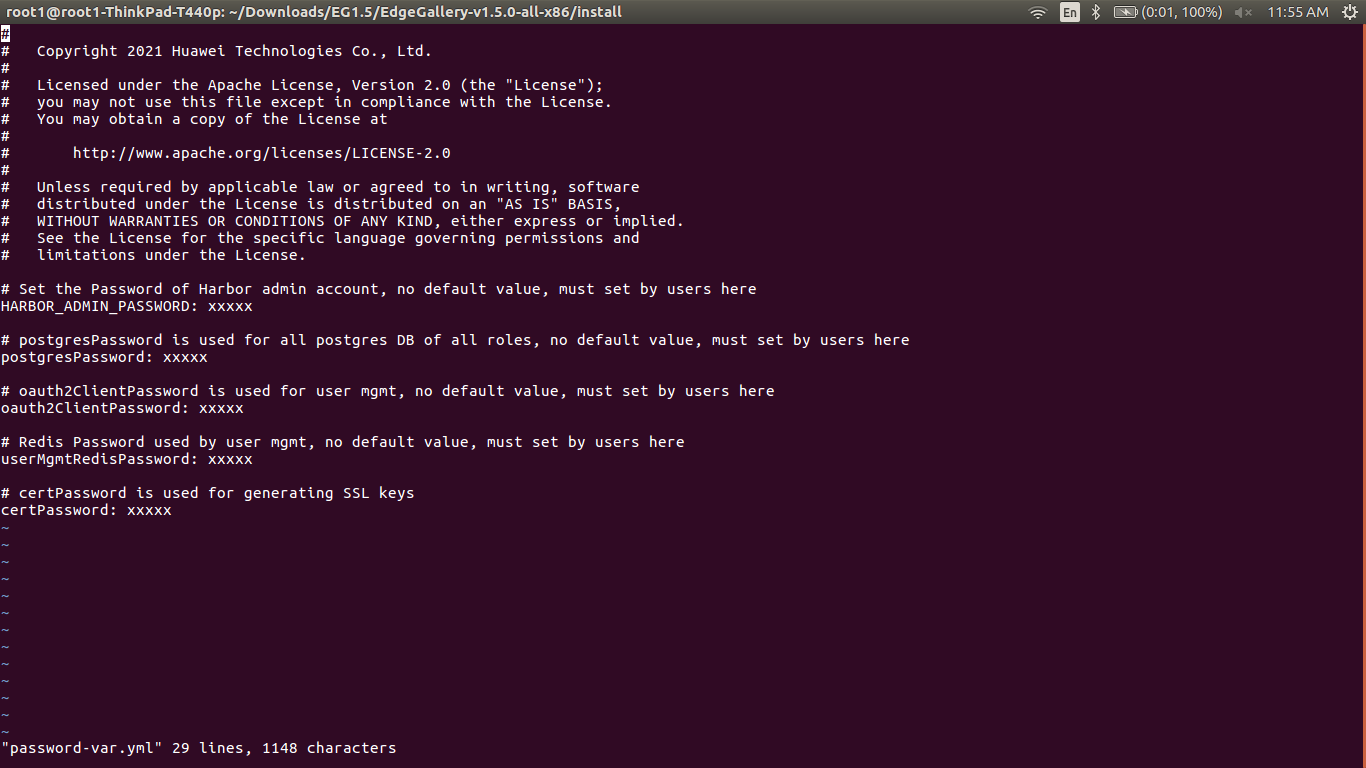
ealt-edge/ocd/infra/playbooks/passwordhosts-var.ymlaio
- Here user can use the private IP of a node
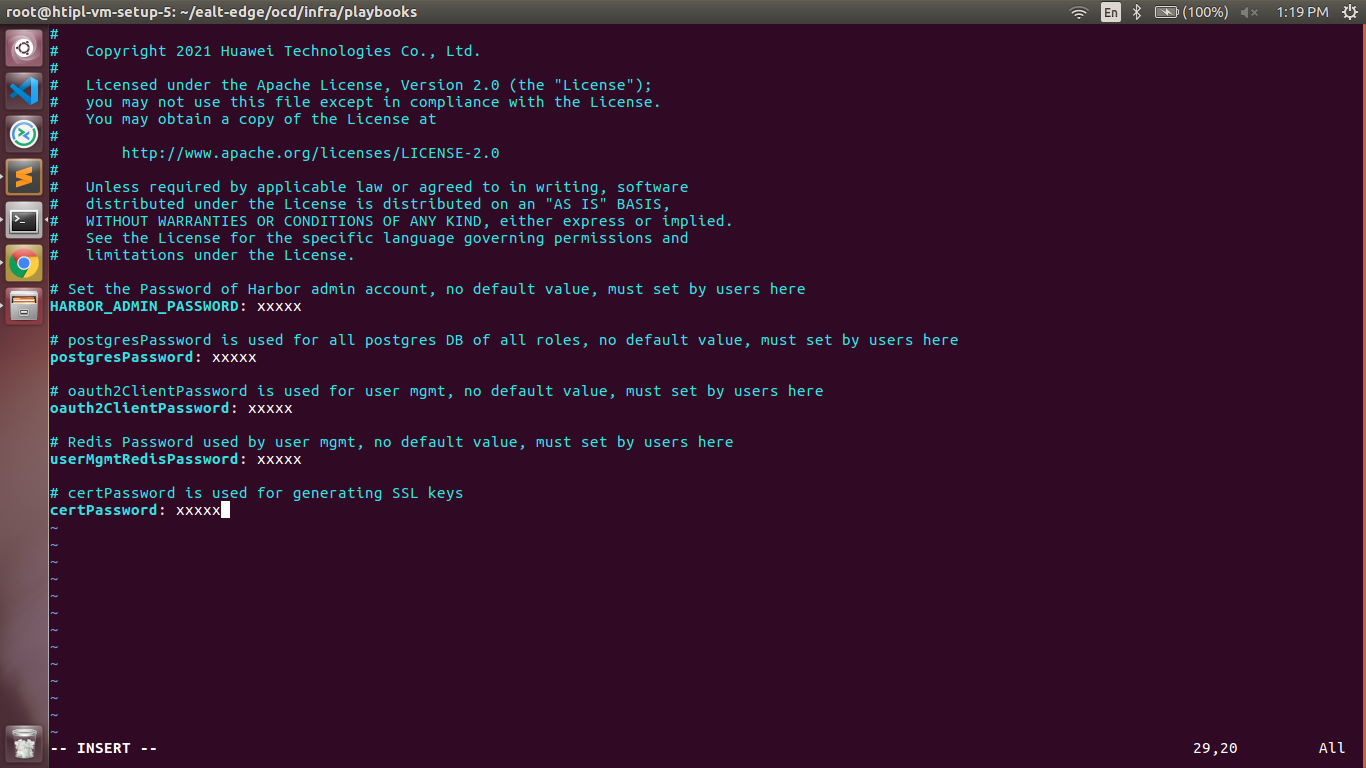
- All passwords must include capital letters, lowercase letters, numbers and special characters and whose length must be no less than 8 characters. Also there should be no special characters
&in it. Otherwise, the deployment will failed because of these simple passwords. - A sample password could be "Harbor@12345"
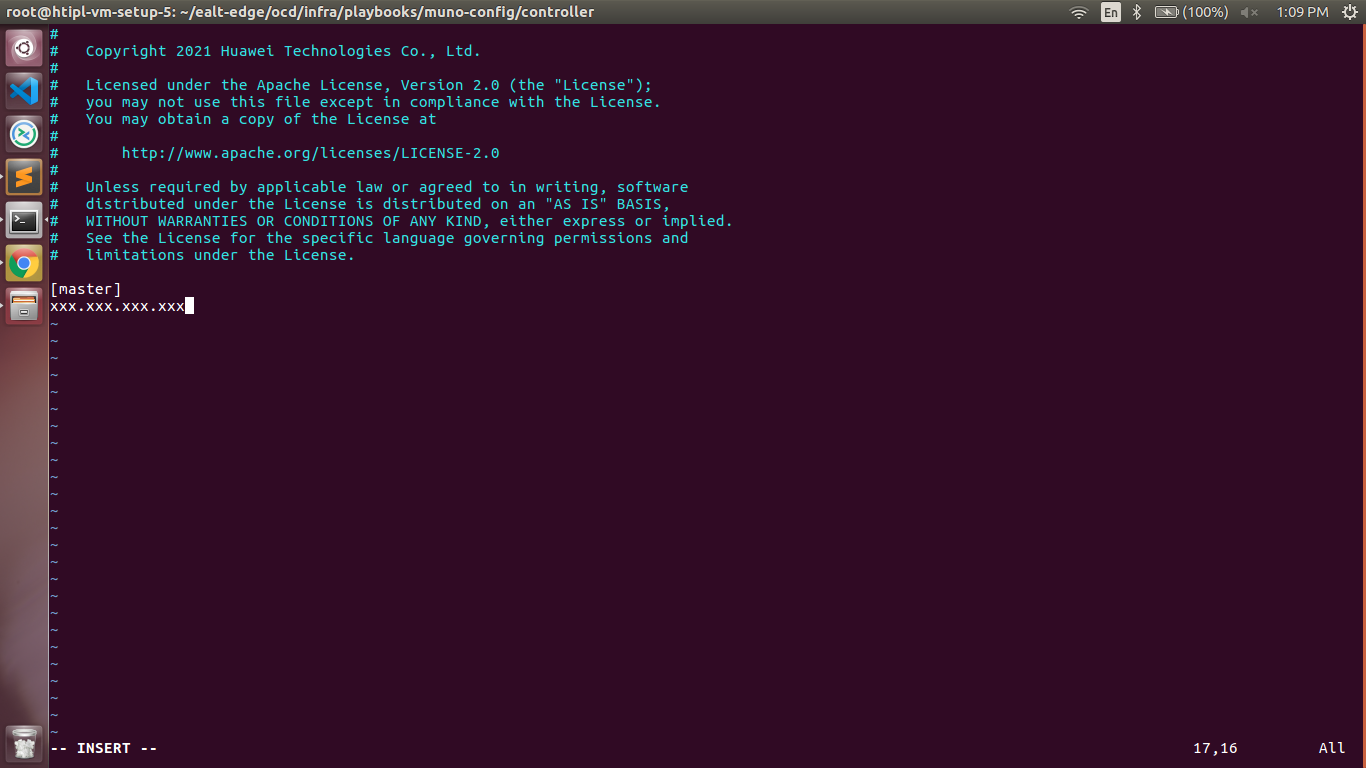
For EdgeGallery MUNO Mode: ealt-edge/ocd/infra/playbooks/muno-config/controller/hosts-muno-controller
- Here user can use the private IP as a master IP of a Controller node
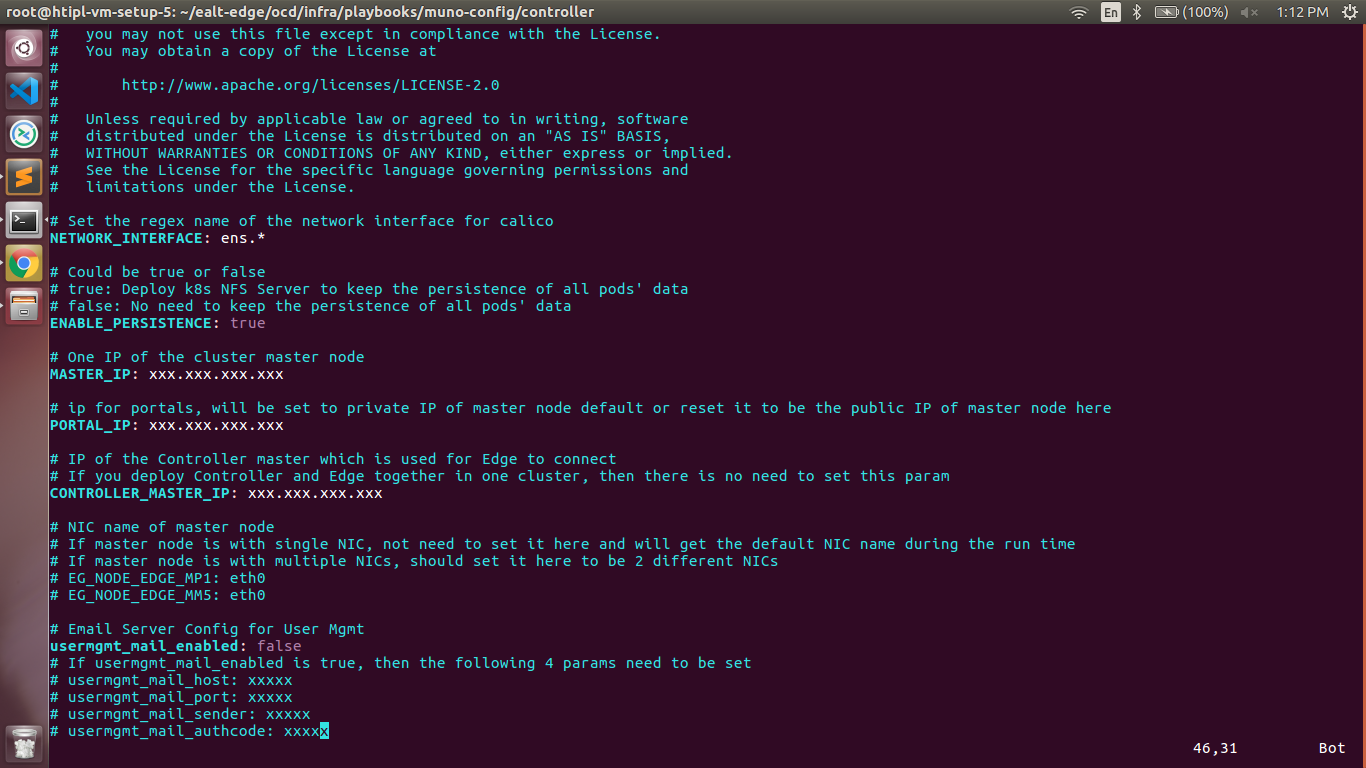
ealt-edge/ocd/infra/playbooks/muno-config/controller/var.yml
var.yml
- NETWORKNETWORK_INTERFACE: regex for network interface on the VM. (user can be check ineterrface name by ifconfig and provide inerface name accordingly for example like eth.* )
- MASTER_IP: Here user can use the private IP as of a MASTER_IP node
- PORTAL PORTAL_IP: If portal need to be access over internet then uncomment the PORTAL_IP and use public IP as a PORTAL_IP otherwise portal will be accessible only on private IP default.
CONTROLLER_MASTER_IP: IP of the Controller master which is used for Edge to connect
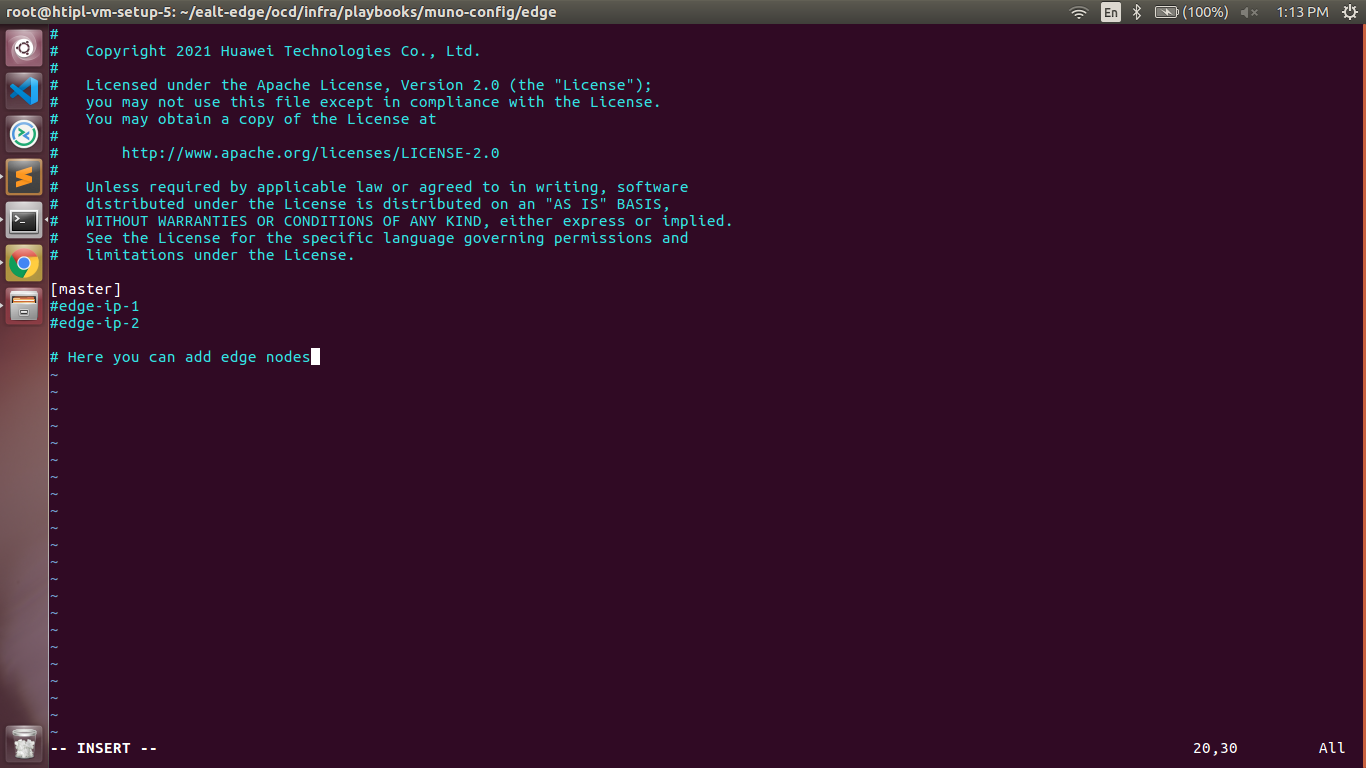
ealt-edge/ocd/infra/playbooks/muno-config/edge/hosts-muno-edge
- Here user can use the private IP as a master IP of a Edge node
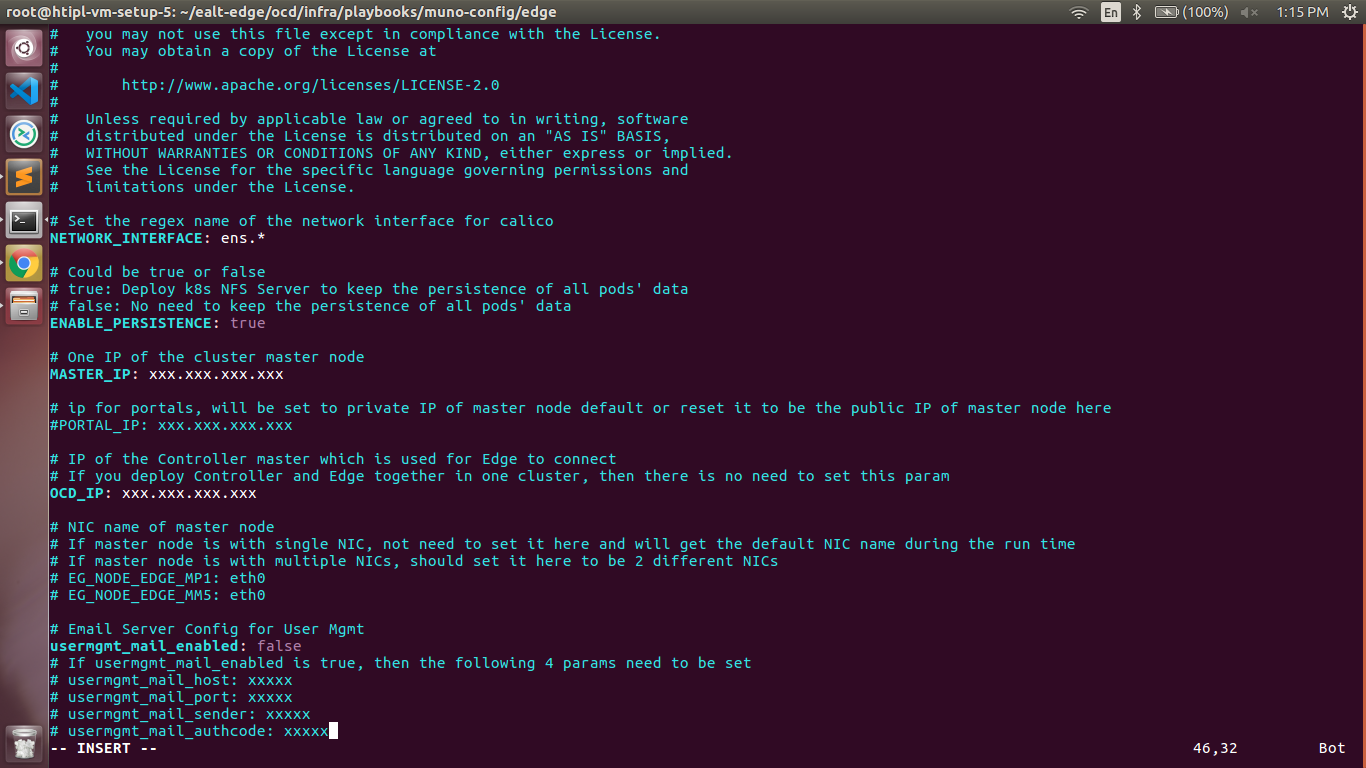
ealt-edge/ocd/infra/playbooks/munopassword-config/edge/var.yml
- NETWORK_INTERFACE: regex for network interface on the VM. (user can be check ineterrface name by ifconfig and provide inerface name accordingly for example like eth.* )
- MASTER_IP: Here user can use the private IP as a MASTER_IP
- PORTAL_IP: If portal need to be access over internet then uncomment the PORTAL_IP and use public IP as a PORTAL_IP otherwise portal will be accessible only on private IP default.
- OCD_IP: Here user can use the private IP od a Controller Node
- All passwords must include capital letters, lowercase letters, numbers and special characters and whose length must be no less than 8 characters. Also there should be no special characters
&in it. Otherwise, the deployment will failed because of these simple passwords. - A sample password could be "Harbor@12345"
For EdgeGallery MUNO Mode:
ealt-edge/ocd/infra/playbooks/muno-config/controller/hosts-muno-controller
- Here user can use the private IP as a master IP of a Controller node
ealt-edge/ocd/infra/playbooks/passwordmuno-config/controller/var.yml
- NETWORK_INTERFACE: regex for network interface on the VM. (user can be check ineterrface name by ifconfig and provide inerface name accordingly for example like eth.* )
- MASTER_IP: Here user can use the private IP of a controller node
- PORTAL_IP: If portal need to be access over internet then uncomment the PORTAL_IP and use public IP of a controller node as a PORTAL_IP otherwise portal will be accessible only on private IP default.
CONTROLLER_MASTER_IP: Private IP of the Controller node.
- All passwords must include capital letters, lowercase letters, numbers and special characters and whose length must be no less than 8 characters. Also there should be no special characters
&in it. Otherwise, the deployment will failed because of these simple passwords. - A sample password could be "Harbor@12345"
For EALT-EDGE stack:
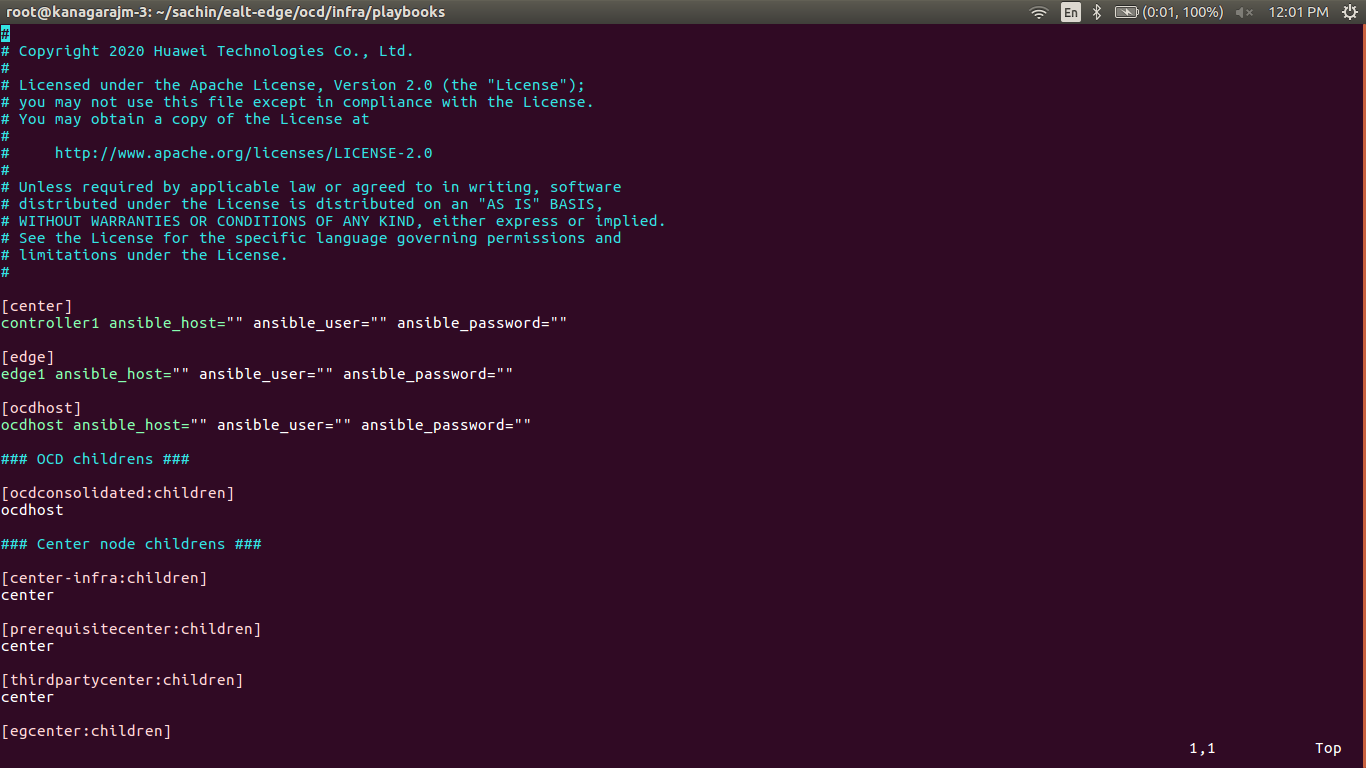
ealtealt-edge/ocd/infra/playbooks/ealt-inventory.ini * Here user can put the public IP in center, edge, ocdhost./muno-config/edge/hosts-muno-edge
- Here user can use the private IP as a master IP of a Edge node
Installing Mode : EALTEdge using Ansible-Playbooks
1. git clone the ealt-edge repo, to download the software to install the EALTEdge Environment.
root@akraino-mec-0001:~# git clone "https://gerrit.akraino.org/r/ealt-edge"
2. go to the below directory
root@akraino-mec-0001:~# cd ealt-edge/ocd/infra/playbooks
3. Modify the Configuration File :
ealt-inventory.ini with the details of CENTER and EDGE Nodes.
For Edge Gallery installation:
MUNO-Mode:
Execute the below command:
ealt-edge/ocd/infra/playbooks/muno-config/edge/var.yml
- NETWORK_INTERFACE: regex for network interface on the VM. (user can be check ineterrface name by ifconfig and provide inerface name accordingly for example like eth.* )
- MASTER_IP: Here user can use the private IP of a edge node
- OCD_IP: Here user can use the private IP of a Controller Node which is used for Edge to connect
ealtcd ealt-edge/ocd/infra/playbooks
ansible-playbook -i muno-config/controller/hosts-muno-controller ealt-eg-muno-controller.yml --extra-vars "operation=install" -e "ansible_user=root"
ansible-playbook -i muno-config/edge/hosts-muno-edge ealt-eg-muno-edge.yml --extra-vars "operation=install" -e "ansible_user=root"
For AIO mode:
Execute the below command
cd ealt-edge/ocd/infra/playbooks
ansible-playbook ealt-eg-aio-latest.yml -i hosts-aio --extra-vars "operation=install" -e "ansible_user=root"
Installation of ealt-edge stack:
ansible-playbook ealt-all.yml -i ealt-inventory.ini --extra-vars "operation=install"
Once the execution is completed in console will see prompt "EALTEdge Environment Installed , Components Install CENTER and EDGE Nodes Successfully"
Snapshot Deployment Overview
N/A
Special Requirements for Virtual Deployments
N/A
Install Jump Host
N/A
Verifying the Setup - VM's
N/A
Upstream Deployment Guide
Upstream Deployment Key Features
N/A
Special Requirements for Upstream Deployments
N/A
Scenarios and Deploy Settings for Upstream Deployments
N/A
Including Upstream Patches with Deployment
N/A
Running
N/A
Interacting with Containerized Overcloud
N/A
Verifying the Setup
Verifying EALTEdge Deployment
Currently the verification is manually done.
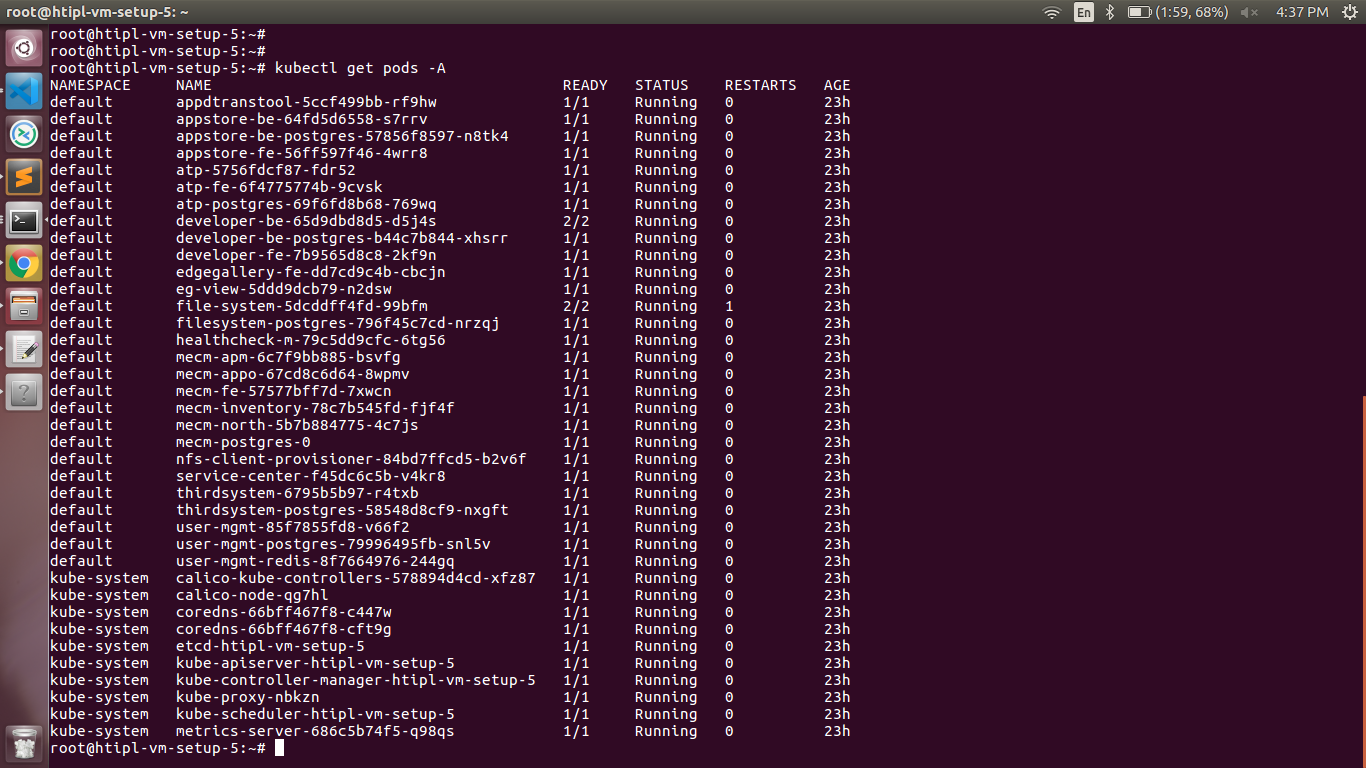
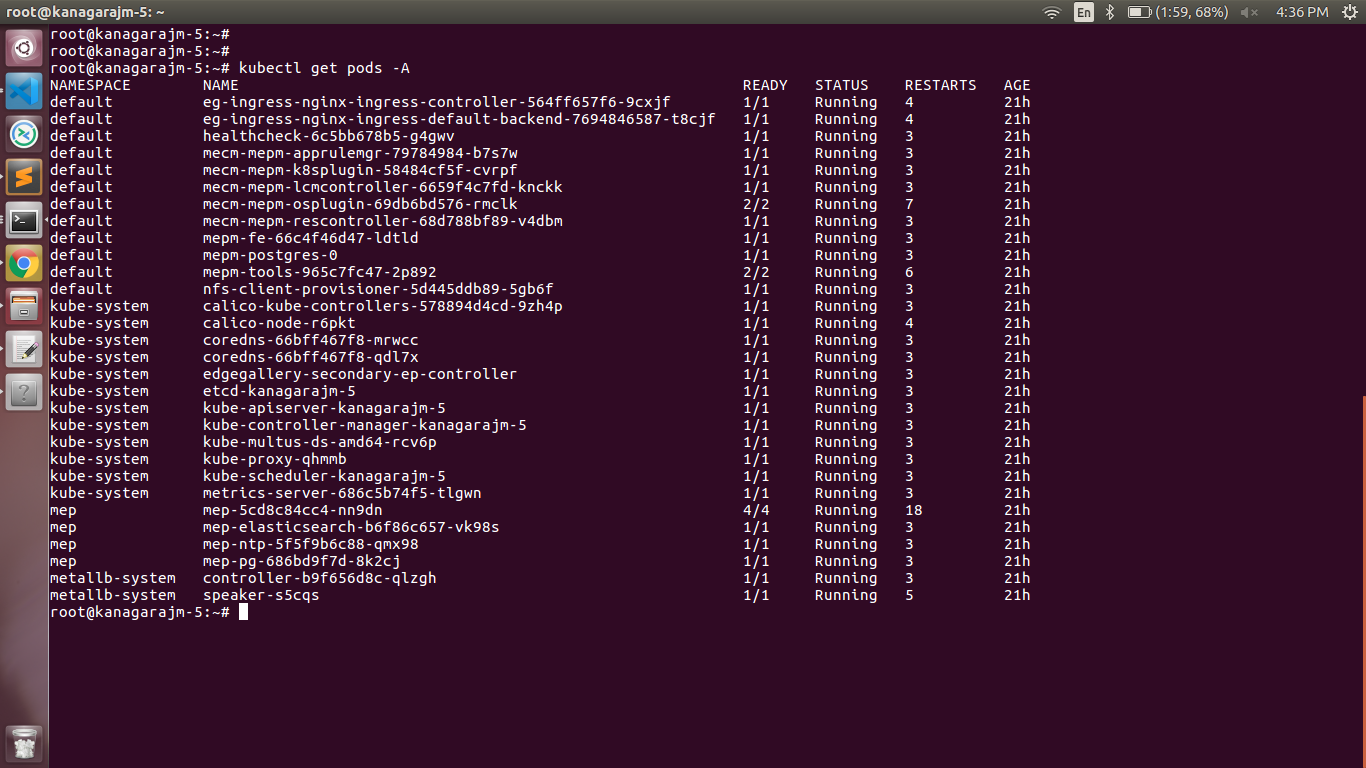
In muno mode
- Login to the Center Node and check whether K8S cluster is installed.
Components and Services running in CENTER Node
Components and Services running EDGE Node
2- Login to the Center Node and check whether K8S cluster is installed in muno mode.
Components and Services running EDGE Node
Deploy Application in EALTEdge
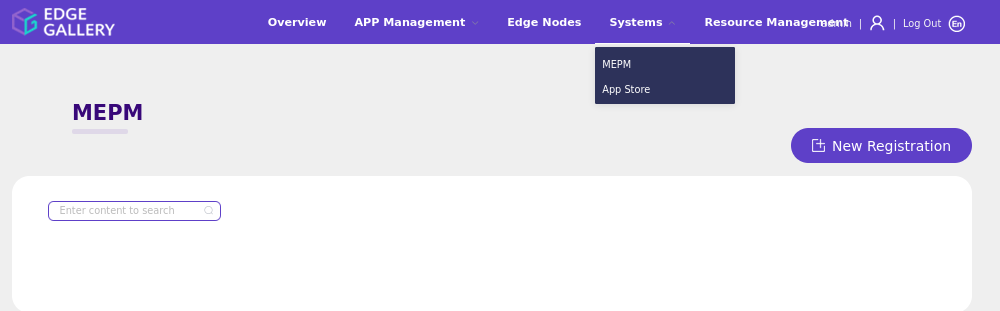
- Login to MECM Portal https://ip:30093
1.1 click on Systems ->App LCM ->New Registration
Name: Applcm(any general name)
IP: applcm"public ip"
Port: 30204
1.2. click on Systems ->App Store ->New Registration
App Store Name: appstore(any general name)
IP: Appstore public ip
Port: 30099
Appstore Repo: {HarborIP:443}(192.168.1.1:443)
Repo Name: appstore(any general name)
Repo Username: admin(harbor user name)
/password-var.yml
- All passwords must include capital letters, lowercase letters, numbers and special characters and whose length must be no less than 8 characters. Also there should be no special characters
&in it. Otherwise, the deployment will failed because of these simple passwords. - A sample password could be "Harbor@12345"
For EALT-EDGE stack:
ealt-edge/ocd/infra/playbooks/ealt-inventory.ini
* Here user can put the public IP in center, edge, ocdhost node.
Installing Mode : EALTEdge using Ansible-Playbooks
1. git clone the ealt-edge repo, to download the software to install the EALTEdge Environment.
root@akraino-mec-0001:~# git clone "https://gerrit.akraino.org/r/ealt-edge"
2. go to the below directory
root@akraino-mec-0001:~# cd ealt-edge/ocd/infra/playbooks
3. Modify the Configuration File :
ealt-inventory.ini with the details of CENTER and EDGE Nodes.
For Edge Gallery installation:
MUNO-Mode:
Execute the below command:
cd ealt-edge/ocd/infra/playbooks
ansible-playbook -i muno-config/controller/hosts-muno-controller ealt-eg-muno-controller.yml --extra-vars "operation=install" -e "ansible_user=root"
ansible-playbook -i muno-config/edge/hosts-muno-edge ealt-eg-muno-edge.yml --extra-vars "operation=install" -e "ansible_user=root"
For AIO mode:
Execute the below command
cd ealt-edge/ocd/infra/playbooks
ansible-playbook ealt-eg-aio-latest.yml -i hosts-aio --extra-vars "operation=install" -e "ansible_user=root"
Installation of ealt-edge stack:
ansible-playbook ealt-all.yml -i ealt-inventory.ini --extra-vars "operation=install"
Once the execution is completed in console will see prompt "EALTEdge Environment Installed , Components Install CENTER and EDGE Nodes Successfully"
Snapshot Deployment Overview
N/A
Special Requirements for Virtual Deployments
N/A
Install Jump Host
N/A
Verifying the Setup - VM's
N/A
Upstream Deployment Guide
Upstream Deployment Key Features
N/A
Special Requirements for Upstream Deployments
N/A
Scenarios and Deploy Settings for Upstream Deployments
N/A
Including Upstream Patches with Deployment
N/A
Running
N/A
Interacting with Containerized Overcloud
N/A
Verifying the Setup
Verifying EALTEdge Deployment
Currently the verification is manually done.
In muno mode
1- Login to the Center Node and check whether K8S cluster is installed.
Components and Services running in Controller Node
Components and Services running EDGE Node
Deploy Application in EALTEdge
- Login to MECM Portal https://ip:30093
1.1 click on Systems ->App LCM ->New Registration Repo Password: Harbor@edge(harbor password)
Vendor Name: vendor Applcm(any general name)
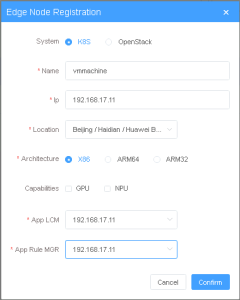
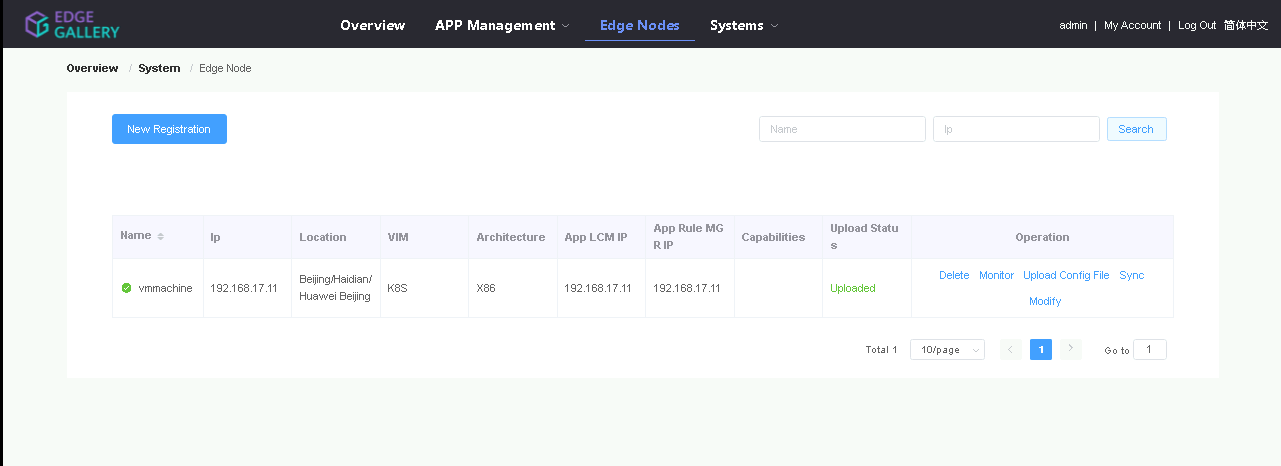
2. log in to MECM Portal https://ip:30093 2.1. Add k8s node: IP: applcm"public ip"
Click on Edge Nodes ->New Rgistration Port: 30204
System: k8s 1.2. click on Systems ->App Store ->New Registration
Name: edge1 App Store Name: appstore(any general name)
IP: edge Appstore public IPip
Location: Select from the drop-down Port: 30099
Architecture: x86 Appstore Repo: {HarborIP:443}(192.168.1.1:443)
Capabilities: select none Repo Name: appstore(any general name)
App LCM: Select edge IP from the drop-down boxRepo Username: admin(harbor user name)
App Rule MGR: Select edge IP from the drop-down box
2.2. Download /root/.kube/config file from edge node Repo Password: Harbor@edge(harbor password)
And click on Upload config file to upload.
Vendor: vendor(any general name)
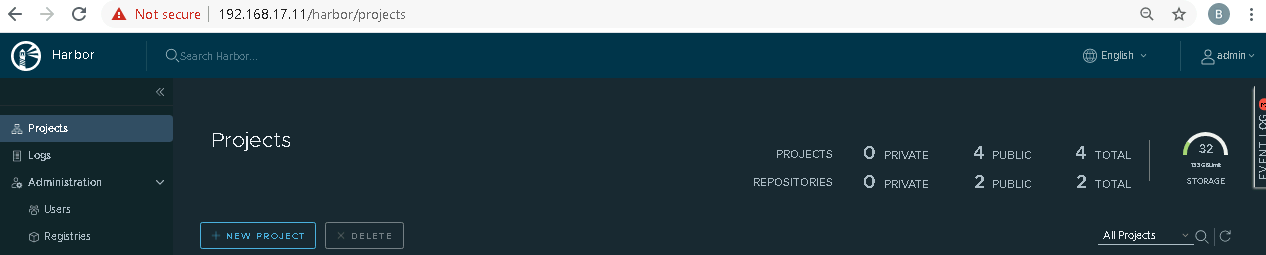
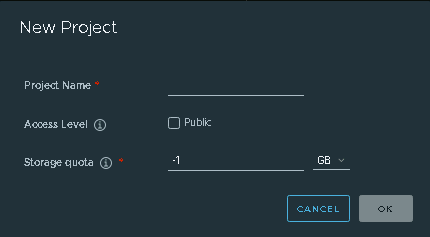
23. log in to harbor MECM Portal https://ip:44330093
3 2.1. Add three new projects
Add k8s node:
Click on Edge Nodes ->New Rgistration
System: k8s
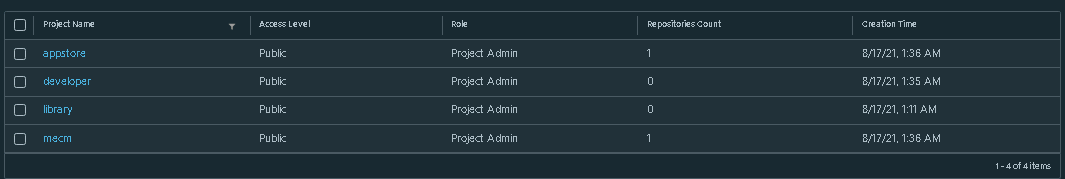
3.2. Those three projects' names are appstore, developer, and mecm. And select access level to the public.
3.3. Final page will look like the below screenshot. Name: edge1(any general name)
4. log in to Developer Portal https://ip:30092 4.1. Add sandbox env to deploy application before publishing IP: edge public IP
Location: Select from the drop-down
Click System ->Host Management ->Add Host . Architecture: x86
Name: general name System Capabilities: k8sselect none
Lcmip: sandbox ip(for testing purpose can provide edge ip, if no sandbox env) mecHost: sandbox ip(for testing purpose can provide edge ip, if no sandbox env) App LCM: Select edge IP from the drop-down box
Port: 30204 App Rule MGR: Select edge IP from the drop-down box
Protocol: https 2.2. Download /root/.kube/config file from edge node
Architecture: X86 Status: And click on Upload config file to upload.
3. log in to harbor Portal https://ip:443
Normal Port Range: leave as it is 3.1. Add three new projects
Address: Bangalore 3.2. Those three projects' names are appstore, developer, and mecm. And select access level to the public.
UploadConfig File: upload sandboxenvkubeconfig file
4.2 Click on Workspace -> Create Project -> Application Integration -> Start
- Go to Application Integration
3.3. Final page will look like the below screenshot.
4. log in to Developer Portal https://ip:30092
- Provide App Name, Version, Provider, Workload Type, Architecture, Industry, Type. 4.1. Add sandbox env to deploy application before publishing
- Upload Icon, provide Description. And click on confirm.
Click System ->Host Management ->Add Host
4.3. Now click on Deployment Test. - Upload Docker images directly from the portal by clicking on Upload App Image.
...
.
...
After that you can take tar file from path and Name: general name
upload image. Or, directly push Docker images to Harbor repo (takes lesser time, preferred). Following command for pushing an image in Harbor:
...
System: k8s
Lcmip: sandbox ip(for testing purpose can provide edge ip, if no sandbox env)
mecHost: sandbox ip(for testing purpose can provide edge ip, if no sandbox env)
Port: 30204
Protocol: https
Architecture: X86
Status: Normal
- Click next, upload deployment yaml file now.
- After config upload, click next and click start deployment
- After Deployment is successful, click on Release Recourses
Note: Port Range: leave as it is
- While Deployment test if any error happens, open ATP portal (https://ip:30094) in another tab of the browser, sign in, come back to the developer portal and re run deployment test Address: Bangalore
UploadConfig File: upload sandboxenvkubeconfig file
- gitee.com/edgegallery/applications repo provides A lot of applications with their logo, deployment YAML & user guides 3.4. Now click on Application Release4.2 Demonstration of application Development & Deployment
Application Development
link - https://www.youtube.com/watch?v=AjQNG5d3p84&t=23s
Upload file for Application Description
Click save config
Application Deployment
Click Next Step, click Start Test, scroll down to find & click the Start Test button, then confirm. Once the testing is complete click on Next Step
click publish to publish an application to AppStore. Go to https://<IP>:30091 and App Warehouse to confirm that the application is successfully ported. link - https://www.youtube.com/watch?v=PbxKpslVnmc&t=31s
Developer Guide and Troubleshooting
...
| S. No | Software | Type | Version | License Information | Remarks |
| 1. | Docker | CRI | 18.09 | Apache 2.0 license | No code modifications done |
| 2. | K8s | Orchestration | 1.18.7 | Apache 2.0 license | No code modifications done |
| 3. | Edge Gallery | Opensource MEC platform | 1.1.1 | Apache 2.0 license | Open Source MEC Platform |
References
Demonstration of application Development & Deployment
Application Development
link - https://www.youtube.com/watch?v=AjQNG5d3p84&t=23s
...
Definitions, acronyms and abbreviations
...