This page intend to list bunch of scenarios for our SD-EWAN case, including the decomposed scenarios and the overall integrated scenario.
| Table of Contents |
|---|
Decomposed scenarios
Decomposed Scenario A: Site-to-Site tunnel with static public IP address
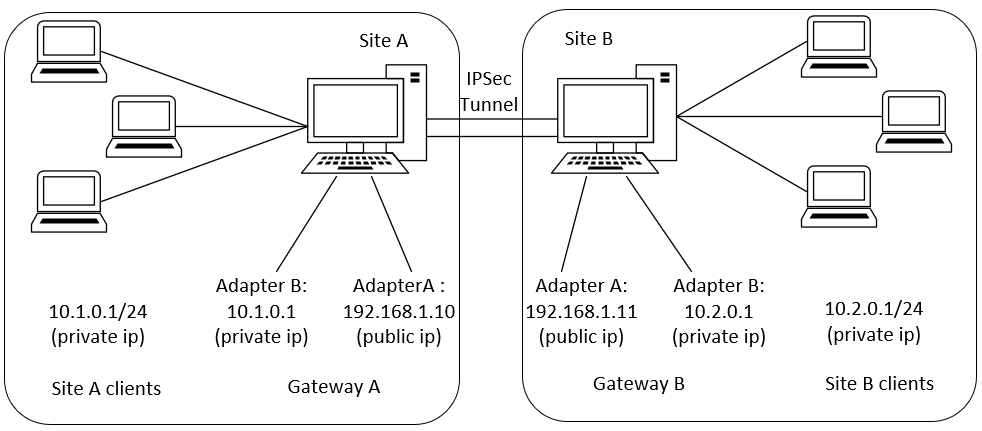
In this scenario, both sites have static public IP address and setup a tunnel between sites. After the tunnel is established, the clients within the site should be able to ping the clients on the other side through the tunnel. The tunnel is authenticated through pre-shared key.
...
Scenario Description:
| Code Block | ||||||
|---|---|---|---|---|---|---|
| ||||||
apiVersion: sdewan.akraino.org/v1alpha1
kind: IPSecSite
metadata:
name: siteA
spec:
node: node1
gateway: 192.168.1.11
pre_shared_key: test123
auth_method: psk
local_identifier: @moon.strongswan.org
remote_identifier: @sun.strongswan.org
crypto_proposal: proposal1
force_crypto_proposal: true
connection:
- name: connA
type: tunnel
mode: start
local_subnet: 10.1.0.1/24
local_sourceip: 192.168.1.10
local_firewall: yes
remote_subnet: 10.2.0.1/24
remote_firewall: yes
keyexchange: ikev2
crypto_proposal: proposal1
proposals:
- name: proposal1
encryption_algorithm: aes128
hash_algorithm: sha256
dh_group: modp3072 |
IPSec CR for gateway B:
Tunnel between site A and site B
Suppose there are two sites A and B. A comes with the subnet 10.1.0.1/24, B comes with the subnet 10.2.0.1/24
Gateway for A is 192.168.1.10
Gateway for B is 192.168.1.11
A and B would like to establish a tunnel
10.1.0.1/24 == 10.2.0.1/24
CRs for the scenario
| Code Block | ||||||
|---|---|---|---|---|---|---|
| ||||||
apiVersion: sdewan.akraino.org/v1alpha1
kind: IpsecProposal
metadata:
name: test_proposal_1
namespace: default
labels:
sdewanPurpose: cnf-1
spec:
encryption_algorithm: aes128
hash_algorithm: sha256
dh_group: modp3072
status:
appliedVersion: "1"
appliedTime: "2020-04-12T09:28:38Z"
inSync: True
|
| Code Block | ||||||
|---|---|---|---|---|---|---|
| ||||||
apiVersion: sdewan.akraino.org/v1alpha1
kind: IpsecSite
metadata:
name: siteA
namespace: default
labels:
sdewanPurpose: cnf-1
spec:
remote: 192.168.1.11
authentication_method: psk
pre_shared_key: test123
crypto_proposal:
- test_proposal_1
connections:
- connection_name: connection_A
type: tunnel
mode: start
local_subnet: 10.1.0.1/24
remote_subnet: 10.2.0.1/24
crypto_proposal:
- test_proposal_1
status:
appliedVersion: "1"
appliedTime: "2020-04-12T09:28:38Z"
inSync: True |
| Code Block | ||||||
|---|---|---|---|---|---|---|
| ||||||
apiVersion: sdewan.akraino.org/v1alpha1
kind: IpsecSite
metadata:
name: siteB
namespace: default
labels:
sdewanPurpose: cnf-1
spec:
remote | ||||||
| Code Block | ||||||
| ||||||
apiVersion: sdewan.akraino.org/v1alpha1 kind: IPSecSite metadata: name: siteB spec: node: node2 gateway: 192.168.1.10 pre_shared_key: test123 auth_method: psk local_identifier: @moon.strongswan.org remote_identifier: @sun.strongswan.org crypto_proposal: proposal1 force_crypto_proposal: true connection: - name: connA type: tunnel mode: start local_subnet: 10.2.0.1/24 local_sourceip: 192.168.1.1110 local_firewallauthentication_method: yespsk remote_subnet: 10.1.0.1/24pre_shared_key: test123 remotecrypto_firewallproposal: yes keyexchange: ikev2 crypto_proposal: proposal1- test_proposal_1 proposalconnections: - connection_name: proposal1connection_B encryption_algorithmtype: aes128tunnel hash_algorithmmode: sha256start dhlocal_group: modp3072 |
NAT CR:
...
Rest calls:
Sites settings
GET /cgi-bin/luci/sdewan/ipsec/v1/sites
subnet: 10.2.0.1/24
remote_subnet: 10.1.0.1/24
crypto_proposal:
- test_proposal_1
status:
appliedVersion: "1"
appliedTime: "2020-04-12T09:28:38Z"
inSync: True |
Rest calls
Sites settings
GET /cgi-bin/luci/sdewan/ipsec/v1/sites
{ { { { "name": “siteA", "gateway":"192.168.1.11", "crypto_proposal": "proposal1", "pre_shared_key": "test123", "authentication_method": "psk", "local_identifiername": “siteA"@moon.strongswan.org", "remote_identifier":"@sun192.168.strongswan1.org11", "connectionscrypto_proposal": ["test_proposal_1", "pre_shared_key": "test123", "authentication_method": "psk", "connections": [ { "name": "connection_A { "name": "connA", "type": "tunnel", "mode": "start", "local_subnet": "10.1.0.1/24", "remote_subnet": "10.2.0.1/24", "crypto_proposal": "proposal1test_proposal_1" } ] }, { "name": "siteB", "gateway":"192.168.1.10", "crypto_proposal": "proposal1test_proposal_1", "pre_shared_key": "test123", "authentication_method": "psk", "remote_identifier": "@moon.strongswan.org", "local_identifier": "@sun.strongswan.org", "connections": [ { "name": "connAconnection_B", "type": "tunnel", "mode": "start", "local_subnet": "10.2.0.1/24", "remote_subnet": "10.1.0.1/24", "crypto_proposal": "proposal1test_proposal_1" } ] } ] |
|---|
...
{ "proposals": [ { "name": "proposal1", "crypto_algorithm": "aes128", "hash_algorithm": "sha256", "dh_group": "modp3072" } ] } |
|---|
Decomposed Scenario B: Host-to-Site
...
tunnel when the initiator requests an overlay IP
In this scenario, the initiator sends out a request to the responderthe responder(either a site gateway/remote host) which has a static public ip address(or dynamic pubic IP with static domain name) in order to setup a tunnel between. However, this time, the roadwarrior is also going to ask for a virtual IP that assigned by the responder. After the tunnel is established, the roadwarrior should be able to get an overlay IP and ping the clients on the other side through the tunnel. The tunnel is authenticated through pre-shared key.
IPSec CR for Gateway A:
| Code Block | ||||||
|---|---|---|---|---|---|---|
| ||||||
apiVersion: sdewan.akraino.org/v1alpha1
kind: IPSecSite
metadata:
name: siteA
spec:
node: node1
gateway: 192.168.1.15
pre_shared_key: test123
auth_method: psk
local_identifier: @sun.strongswan.org
remote_identifier: @roadwarrior.strongswan.org
crypto_proposal: proposal1
force_crypto_proposal: true
connection:
- name: connA
type: tunnel
mode: start
local_subnet: 10.1.0.1/24
local_sourceip: 192.168.1.10
remote_sourceip: 192.168.1.15
crypto_proposal: proposal1
proposal:
- name: proposal1
encryption_algorithm: aes128
hash_algorithm: sha256
dh_group: modp3072 |
IPSec CR for roadwarrior(initiator):
Scenario Description:
Tunnel between site A and host B(Responder and Initiator)
Suppose there is one site A and one host B. A comes with the subnet 10.1.0.1/24.
Gateway for A is 192.168.1.10 which is a public ip address
Host B has no public address and want to request one from the peer(suppose the vip assigned is 10.3.0.12)
A and B would like to establish a tunnel
10.1.0.1/24 == 10.3.0.12/32
CRs for the scenario
| Code Block | ||||||
|---|---|---|---|---|---|---|
| ||||||
apiVersion: sdewan.akraino.org/v1alpha1
kind: IpsecProposal
metadata:
name: test_proposal_1
namespace: default
labels:
sdewanPurpose: cnf-1
spec:
encryption_algorithm: aes128
hash_algorithm: sha256
dh_group: modp3072
status:
appliedVersion: "1"
appliedTime: "2020-04-12T09:28:38Z"
inSync: True
|
| Code Block | ||||||
|---|---|---|---|---|---|---|
| ||||||
apiVersion: sdewan sdewan.akraino.org/v1alpha1 kind: IPSecSite IpsecSite metadata: name: siteA namenamespace: roadwarriordefault spec labels: node sdewanPurpose: roadwarriorcnf-1 spec: gatewayremote: 192.168.1.10%any preauthentication_shared_keymethod: test123psk authpre_shared_methodkey: psktest localcrypto_identifierproposal: @roadwarrior.strongswan.org remote_identifier: @sun.strongswan.org - cryptotest_proposal: "proposal1"_1 force_crypto_proposal: trueconnections: connection: - connection_name: connAconnection_A type: tunnel mode: start local_sourceipsubnet: 19210.1681.10.151/24 remote_subnetsourceip: 10.13.0.1/24 remote_sourceip: 192.168.1.10 crypto_proposal: proposal1 proposal: - name: proposal1test_proposal_1 status: encryption_algorithmappliedVersion: aes128"1" hash_algorithm: sha256 dh_group: modp3072 |
NAT CR:
...
Rest calls:
Sites settings
GET /cgi-bin/luci/sdewan/ipsec/v1/sites
appliedTime: "2020-04-12T09:28:38Z"
inSync: True |
| Code Block | ||||||
|---|---|---|---|---|---|---|
| ||||||
apiVersion: sdewan.akraino.org/v1alpha1
kind: IpsecHost
metadata:
name: hostB
namespace: default
labels:
sdewanPurpose: cnf-1
spec:
remote: 192.168.1.10
authentication_method: psk
pre_shared_key: test
crypto_proposal:
- test_proposal_1
connections:
- connection_name: connection_A
type: tunnel
mode: start
local_sourceip: %config
remote_subnet: 0.0.0.0/0
crypto_proposal:
- test_proposal_1
status:
appliedVersion: "1"
appliedTime: "2020-04-12T09:28:38Z"
inSync: True |
Rest calls
Sites settings
GET /cgi-bin/luci/sdewan/ipsec/v1/sites
{ { { "name": "siteA", "gateway":"192.168.1.11", "crypto_proposal": "proposal1", "pre_shared_key": "test123", "authentication_method": "psk", "local_identifier": "@moon.strongswan.org", "remote_identifier": "@sun.strongswan.org", "connections": [ { "name": "connA", "type": "tunnel", "mode": "start", "local_subnet": "10.1.0.1/24", "remote_sourceip": "192.168.1.15", "local_sourceip": "192.168.1.10", "crypto_proposal": "proposal1" } ] }, { "name": "roadwarriorsiteA", "gatewayremote":"192.168.1.10%any", "crypto_proposal": "proposal1test_proposal_1", "pre_shared_key": "test123", "authentication_method": "psk", "remotelocal_identifier": "@moon.strongswan.org", "localremote_identifier": "@sun.strongswan.org", "connections": [ { "name": "connA", "type": "tunnel", "mode": "start", "local_sourceipsubnet": "19210.168.1.15", "remote_sourceip": "192.168.1.100.1/24", "remote_subnetsourceip": "10.13.0.1/24", "crypto_proposal": "proposal1test_proposal_1" } ] }, } ] |
|---|
Proposal settings
GET /cgi-bin/luci/sdewan/ipsec/v1/proposals
{ "name": "hostB", "remote":"192.168.1.10", "crypto_proposal": "test_proposal_1", |
|---|
|
|---|
|
|---|
" |
|---|
pre_shared_key": " |
|---|
test123",
|
|---|
" |
|---|
authentication_ |
|---|
method": " |
|---|
psk",
|
|---|
" |
|---|
remote_ |
|---|
identifier": " |
|---|
|
|---|
" |
|---|
local_identifier": "@sun.strongswan.org", "connections": [ { "name": "connA", "type": " |
|---|
tunnel",
|
|---|
|
|---|
}
Decomposed Scenario C: Host-to-Site tunnel when the initiator requests an overlay IP
In this scenario, the initiator sends out a request to the responder(either a site gateway/remote host) which has a static public ip address(or dynamic pubic IP with static domain name) in order to setup a tunnel between. However, this time, the roadwarrior is also going to ask for a virtual IP that assigned by the responder. After the tunnel is established, the roadwarrior should be able to get an overlay IP and ping the clients on the other side through the tunnel. The tunnel is authenticated through pre-shared key.
IPSec CR for Gateway A:
| Code Block | ||||||
|---|---|---|---|---|---|---|
| ||||||
apiVersion: sdewan.akraino.org/v1alpha1
kind: IPSecSite
metadata:
name: siteA
spec:
node: node1
gateway: any
pre_shared_key: test123
auth_method: psk
local_identifier: @moon.strongswan.org
remote_identifier: @roadwarrior.strongswan.org
crypto_proposal: proposal1
force_crypto_proposal: true
connection:
- name: connA
type: tunnel
mode: start
local_subnet: 10.1.0.1/24
local_sourceip: 192.168.1.10
local_firewall: yes
remote_sourceip: 10.3.0.1/24
remote_firewall: yes
crypto_proposal: "proposal1"
proposal:
- name: proposal1
encryption_algorithm: aes128
hash_algorithm: sha256
dh_group: modp3072 |
IPSec CR for roadwarrior(initiator):
"mode": "start", "local_sourceip": "%config", "remote_subnet": "10.1.0.1/24", "crypto_proposal": "test_proposal_1" } ] } ] |
|---|
Proposal settings
GET /cgi-bin/luci/sdewan/ipsec/v1/proposals
{ "proposals": [ { "crypto_algorithm": "aes128", "hash_algorithm": "sha256", "dh_group": "modp3072" } ] } |
|---|
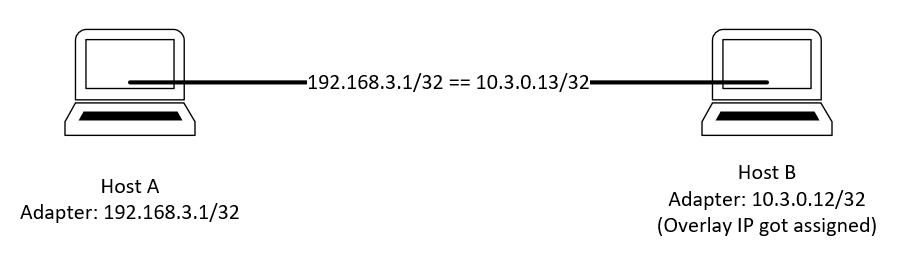
Decomposed Scenario C: Host to host tunnel
Setup a tunnel between the host who got assigned the virtual IP and another host with PIP.
Scenario Description:
Tunnel between host A and host B
Suppose there are two hosts A and B.
A has a public ip which is 192.168.3.1
B is a host which already get a vip 10.3.0.12
A and B would like to establish a tunnel
192.168.3.1/32 == 10.3.0.12/32
CRs for the scenario
| Code Block | ||||||
|---|---|---|---|---|---|---|
| ||||||
apiVersion: sdewan.akraino.org/v1alpha1
kind: IpsecProposal
metadata:
name: test_proposal_1
namespace: default
labels:
sdewanPurpose: cnf-1
spec:
encryption_algorithm: aes128
hash_algorithm: sha256
dh_group: modp3072
status:
appliedVersion: "1"
appliedTime: "2020-04-12T09:28:38Z"
inSync: True
|
| Code Block | ||||||
|---|---|---|---|---|---|---|
| ||||||
apiVersion: sdewan | ||||||
| Code Block | ||||||
| ||||||
apiVersion: sdewan.akraino.org/v1alpha1 kind: IPSecSite IpsecHost metadata: name: hostA namenamespace: roadwarriordefault spec labels: node: roadwarrior gatewaysdewanPurpose: 192.168.1.10cnf-1 spec: pre_shared_keyremote: test123%any authauthentication_method: psk localpre_shared_identifierkey: @roadwarrior.strongswan.orgtest remotecrypto_identifierproposal: @moon.strongswan.org crypto - test_proposal: proposal1_1 force_crypto_proposal: trueconnections: connection: - connection_name: connAconnection_A type: tunnel mode: start local_sourceip: %config local_firewall: yes remote_subnetsourceip: 10.13.0.1/2412 remote crypto_sourceip: 192.168.1.10proposal: remote_firewall: yes - cryptotest_proposal: "proposal1"_1 status: proposalappliedVersion: "1" - name: proposal1appliedTime: "2020-04-12T09:28:38Z" inSync: True |
| Code Block | ||||||
|---|---|---|---|---|---|---|
| ||||||
apiVersion: sdewan.akraino.org/v1alpha1 kind: IpsecHost metadata: name: hostB encryption_algorithmnamespace: aes128default labels: hash_algorithm: sha256 dh_group: modp3072 |
NAT CR:
...
Rest calls:
Sites settings
GET /cgi-bin/luci/sdewan/ipsec/v1/sites
sdewanPurpose: cnf-1
spec:
remote: 192.168.3.1
authentication_method: psk
pre_shared_key: test
crypto_proposal:
- test_proposal_1
connections:
- connection_name: connection_A
type: tunnel
mode: start
local_sourceip: 10.3.0.13
crypto_proposal:
- test_proposal_1
status:
appliedVersion: "1"
appliedTime: "2020-04-12T09:28:38Z"
inSync: True |
Rest calls
Sites settings
GET /cgi-bin/luci/sdewan/ipsec/v1/sites
{
"sites": [
{ "name": "siteA",
"gateway":"192.168.1.11",
"crypto_proposal": "proposal1",
"pre_shared_key": "test123",
"authentication_method": "psk",
"local_identifier": "@moon.strongswan.org",
"remote_identifier": "@sun.strongswan.org",
"connections": [
{ "name": "connA",
"type": "tunnel",
"mode": "start",
"local_subnet": "10.1.0.1/24",
"remote_sourceip": "10.3.0.1/24",
{ { "name": "hostA", "remote":"%any", "crypto_proposal": "test_proposal_1", "pre_shared_key": "test123", "authentication_method": "psk", "local_identifier": "@moon.strongswan.org", |
|---|
" |
|---|
remote_ |
|---|
identifier": " |
|---|
@sun. |
|---|
"connections": [ { "name": "connA", "type": "tunnel", "mode": "start", "remote_sourceip": "10.3.0.12", "crypto_proposal": " |
|---|
test_proposal_1" } ] }, { "name": " |
|---|
hostB", " |
|---|
remote":"192.168.3.1 |
|---|
", "crypto_proposal": " |
|---|
test_proposal_1", "pre_shared_key": "test123", "authentication_method": "psk", "remote_identifier": "@moon.strongswan.org", "local_identifier": "@sun.strongswan.org", "connections": [ { "name": "connA", "type": "tunnel", "mode": "start", "local |
|---|
_sourceip": " |
|---|
10 |
|---|
.3.0. |
|---|
12", "crypto_proposal": " |
|---|
test_proposal_1" } ] } ] |
|---|
Proposal settings
GET /cgi-bin/luci/sdewan/ipsec/v1/proposals
{ "proposals": [ { |
|---|
"crypto_algorithm": "aes128", "hash_algorithm": "sha256", "dh_group": "modp3072" } ] } |
|---|
Targeted Scenarios
...
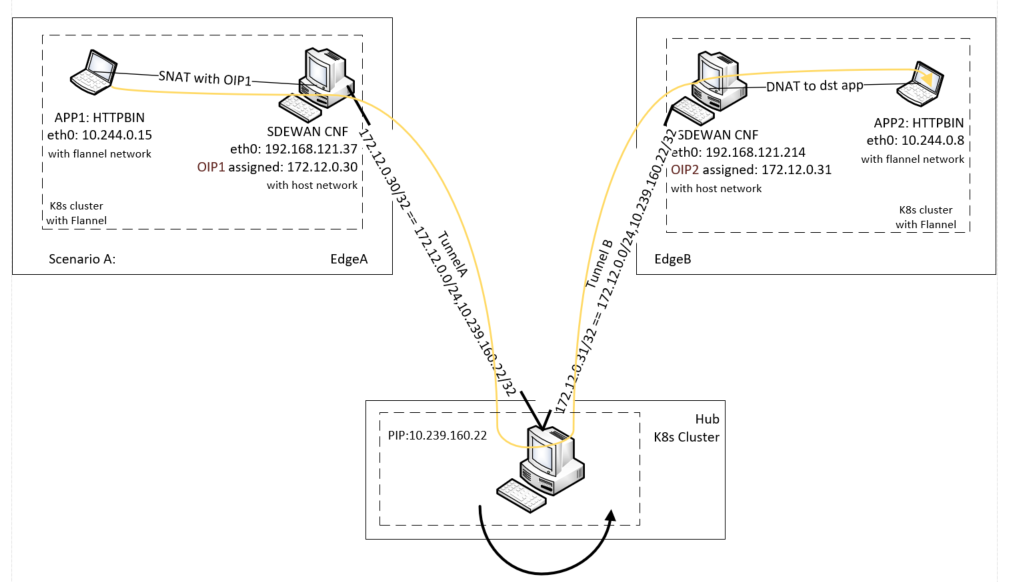
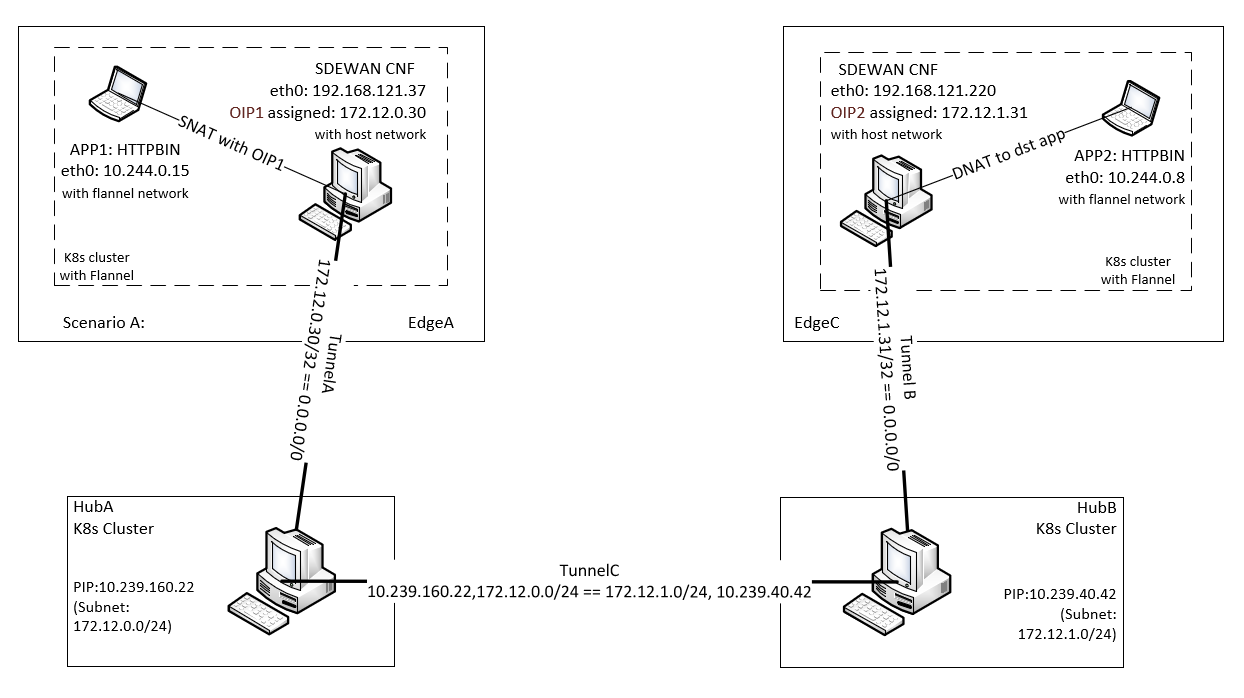
Scenario A: Edge to traffic hub tunnel where inter micro-service communication across edges that attached to same traffic hub.
| Section | |||||||||||||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| |||||||||||||||||||||||||||||||||
|
| Section | |||||||||||||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| |||||||||||||||||||||||||||||||||
|
| Section | |||||||||||||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| |||||||||||||||||||||||||||||||||
|
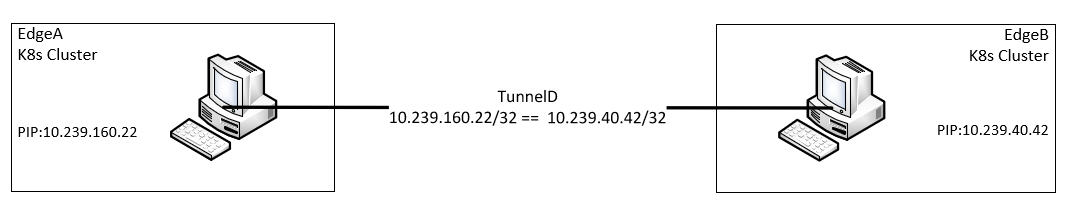
Scenario B: Edge to Edge tunnels when micro-service communication happens across edges without involving hubs
| Section | |||||||||||||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| |||||||||||||||||||||||||||||||||
|
| Section | |||||||||||||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| |||||||||||||||||||||||||||||||||
|
Scenario C: Hub to hub tunnel when inter micro-service communication across edges that attached to different traffic hubs
| Section | |||||||||||||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| |||||||||||||||||||||||||||||||||
|
| Section | |||||||||||||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| |||||||||||||||||||||||||||||||||
|
| Section | |||||||||||||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| |||||||||||||||||||||||||||||||||
|
| Section | |||||||||||||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| |||||||||||||||||||||||||||||||||
|
Overall scenarios
Here shows the overall scenario we want to achieve in the ICN SDEWAN case.
...