...
Targeted Scenarios
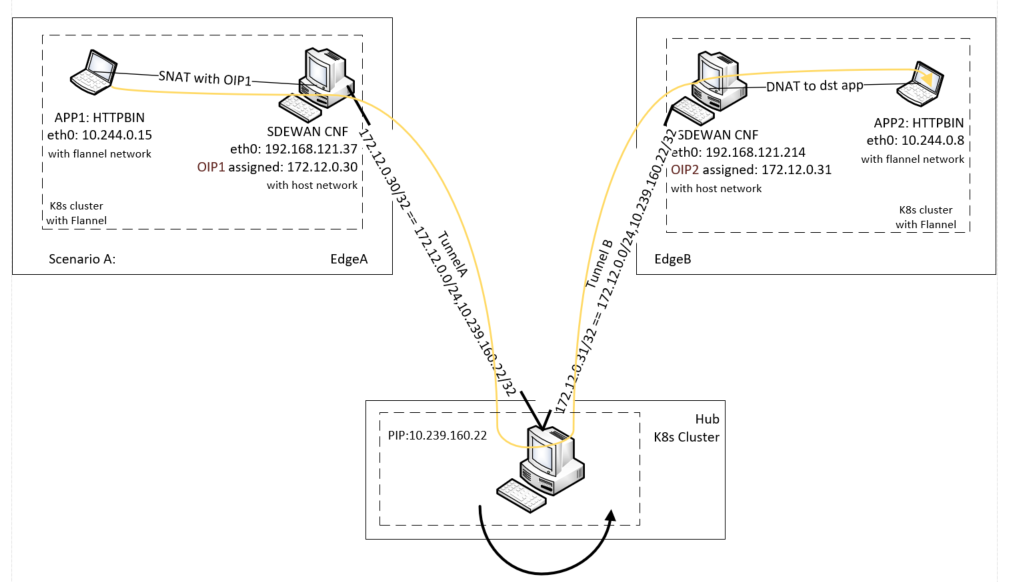
Scenario A: Edge to traffic hub tunnel where inter micro-service communication across edges that attached to same traffic hub.
| Section |
|---|
|
| Column |
|---|
|
| Code Block |
|---|
| language | yml |
|---|
| title | Sample CR for edgeA |
|---|
| collapse | true |
|---|
| CR for sdewan cnf on edgeA:
apiVersion: sdewan.akraino.org/v1alpha1
kind: IpsecHost
metadata:
name: edgeA
namespace: default
labels:
sdewanPurpose: cnf-1
spec:
remote: 10.239.160.22
authentication_method: psk
pre_shared_key: test
crypto_proposal:
- test_proposal_1
connections:
- connection_name: connection_A
type: tunnel
mode: start
local_sourceip: %config
remote_subnet: 0.0.0.0/0, 10.239.160.22/32
crypto_proposal:
- test_proposal_1
status:
appliedVersion: "1"
appliedTime: "2020-04-12T09:28:38Z"
inSync: True |
|
| Column |
|---|
| The CRs defined will then be interpreted into some IPSec configuration that could be recognized by Openwrt and then translate to Strongswan configs |
| Sample CR | edgeBCRonedgeBapiVersion: sdewan.akraino.org/v1alpha1
kind: IpsecHost
metadata:
name: edgeB
namespace: default
labels:
sdewanPurpose: cnf-1
spec:
remote: conn siteA-connA
left=%any
right=10.239.160.22
leftsourceip=%config
rightsubnet=0.0.0.0/0,10.239.160.22/32
|
|
authentication_method: pre_shared_key: testcrypto_proposal: - test_proposal_1
connections:
- connection_name: connection_A
type: tunnel
mode: start
local_sourceip: %configkeyexchange=ikev2
esp=aes192-sha1-modp3072
ike=aes192-sha1-modp3072
type=tunnel
|
|
|
| Section |
|---|
|
| Column |
|---|
|
| Code Block |
|---|
| language | yml |
|---|
| title | Sample CR for edgeB |
|---|
| collapse | true |
|---|
| CR on sdewan cnf on edgeB:
apiVersion: sdewan.akraino.org/v1alpha1
kind: IpsecHost
metadata:
name: edgeB
namespace: default
labels:
sdewanPurpose: cnf-1
spec:
remote: |
|
remote_subnet: 0.0.0.0/0,/32
authentication_method: psk
pre_shared_key: test
crypto_proposal:
|
|
statusappliedVersion:"1"
appliedTime: "2020-04-12T09:28:38Z"connection_name: connection_A
|
|
inSync:True |
| Code Block |
|---|
| language | yml |
|---|
| title | Sample CR for Hub |
|---|
| collapse | true |
|---|
|
CRonsdewan type: tunnel
mode: start
local_sourceip: %config
remote_subnet: 0.0.0.0/0, 10.239.160.22/32
crypto_proposal:
- test_proposal_1
status:
appliedVersion: "1"
appliedTime: "2020-04-12T09:28:38Z"
inSync: True |
|
| Column |
|---|
| The CRs defined will then be interpreted into some IPSec configuration that could be recognized by Openwrt and then translate to Strongswan configs |
| Column |
|---|
|
| Code Block |
|---|
| language | yml |
|---|
| title | Strongswan configs for edgeB |
|---|
| collapse | true |
|---|
| Strongswan configs for sdewan cnf on edgeB:
conn edgeB-connA
left=%any
right=10.239.160.22
leftsourceip=%config
rightsubnet=0.0.0.0/0,10.239.160.22/32
leftauth=psk
rightauth=psk
auto=start
keyexchange=ikev2
esp=aes192-sha1-modp3072
ike=aes192-sha1-modp3072
type=tunnel
|
|
|
| Section |
|---|
|
| Column |
|---|
|
| Code Block |
|---|
| language | yml |
|---|
| title | Sample CR for Hub |
|---|
| collapse | true |
|---|
| CR on sdewan on hub:
apiVersion: sdewan.akraino.org/v1alpha1
kind: IpsecSite
metadata:
name: Hub
namespace: default
labels:
sdewanPurpose: cnf-1
spec:
remote: %any
authentication_method: psk
pre_shared_key: test
crypto_proposal:
- test_proposal_1
connections:
- connection_name: connection_A
type: tunnel
mode: start
local_subnet: 172.12.0.1/24,10.239.160.22/32
remote_sourceip: 172.12.0.1/24
crypto_proposal:
- test_proposal_1
status:
appliedVersion: "1"
appliedTime: "2020-04-12T09:28:38Z"
inSync: True |
|
| Column |
|---|
| The CRs defined will then be interpreted into some IPSec configuration that could be recognized by Openwrt and then translate to Strongswan configs |
| Column |
|---|
|
| Code Block |
|---|
| language | yml |
|---|
| title | Strongswan configs for hub |
|---|
| collapse | true |
|---|
| Strongswan configs for sdewan cnf on hub:
conn tunnel
left=10.239.160.22
leftsubnet=172.12.0.1/24,10.239.160.22/32
rightsourceip=172.12.0.30-172.12.0.45
leftauth=psk
rightauth=psk
auto=start
keyexchange=ikev2
ike=aes192-sha1-modp3072
esp=aes192-sha1-modp3072
type=tunnel
|
|
|
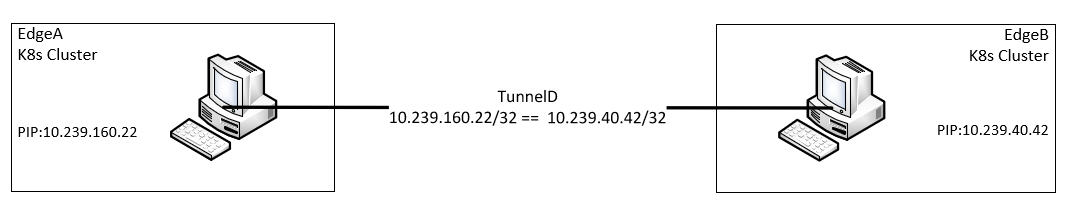
Scenario B: Edge to Edge tunnels when micro-service communication happens across edges without involving hubs
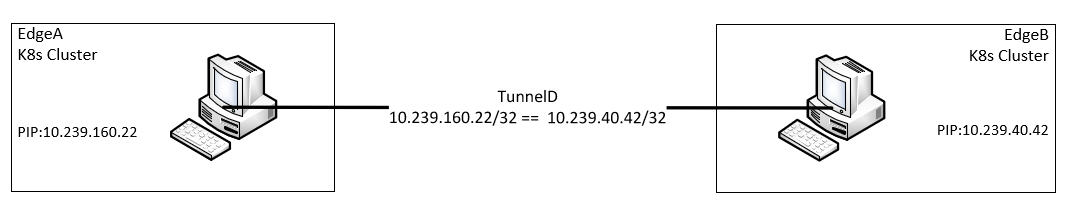 Image Added
Image Added
| Section |
|---|
|
| Column |
|---|
|
| Code Block |
|---|
| language | yml |
|---|
| title | Sample CR for EdgeA |
|---|
| collapse | true |
|---|
| CR on sdewan cnf on edgeA:
apiVersion: sdewan.akraino.org/v1alpha1
kind: IpsecHost
metadata:
name: edgeA
namespace: default
labels:
sdewanPurpose: cnf-1
spec:
remote: 10.239.40.42
authentication_method: psk
pre_shared_key: test
crypto_proposal:
- test_proposal_1
connections:
- connection_name: connection_A
type: tunnel
mode: start
crypto_proposal:
- test_proposal_1
status:
appliedVersion: "1"
appliedTime: "2020-04-12T09:28:38Z"
inSync: True |
|
| Column |
|---|
| The CRs defined will then be interpreted into some IPSec configuration that could be recognized by Openwrt and then translate to Strongswan configs |
| Column |
|---|
|
| Code Block |
|---|
| language | yml |
|---|
| title | Strongswan configs for edgeA |
|---|
| collapse | true |
|---|
| Strongswan configs for sdewan cnf on edgeA:
conn edgeA-connection_A
left=%any
right=10.239.40.42
leftauth=psk
rightauth=psk
auto=start
keyexchange=ikev2
ike=aes192-sha1-modp3072
esp=aes192-sha1-modp3072
type=tunnel
|
|
|
| Section |
|---|
|
| Column |
|---|
|
| Code Block |
|---|
| language | yml |
|---|
| title | Sample CR for EdgeB |
|---|
| collapse | true |
|---|
| CR on sdewan cnf on edgeB:
apiVersion: sdewan.akraino.org/v1alpha1
kind: IpsecHost
metadata:
name: edgeB
namespace: default
labels:
sdewanPurpose: cnf-1
spec:
remote: 10.239.160.22
authentication_method: psk
pre_shared_key: test
crypto_proposal:
- test_proposal_1
connections:
- connection_name: connection_A
type: tunnel
mode: start
crypto_proposal:
- test_proposal_1
status:
appliedVersion: "1"
appliedTime: "2020-04-12T09:28:38Z"
inSync: True |
|
| Column |
|---|
| The CRs defined will then be interpreted into some IPSec configuration that could be recognized by Openwrt and then translate to Strongswan configs |
| Column |
|---|
|
| Code Block |
|---|
| language | yml |
|---|
| title | Strongswan configs for edgeB |
|---|
| collapse | true |
|---|
| Strongswan configs for sdewan cnf on edgeB:
conn edgeB-connection_A
left=%any
right=10.239.160.22
leftauth=psk
rightauth=psk
auto=start
keyexchange=ikev2
ike=aes192-sha1-modp3072
esp=aes192-sha1-modp3072
type=tunnel
|
|
|
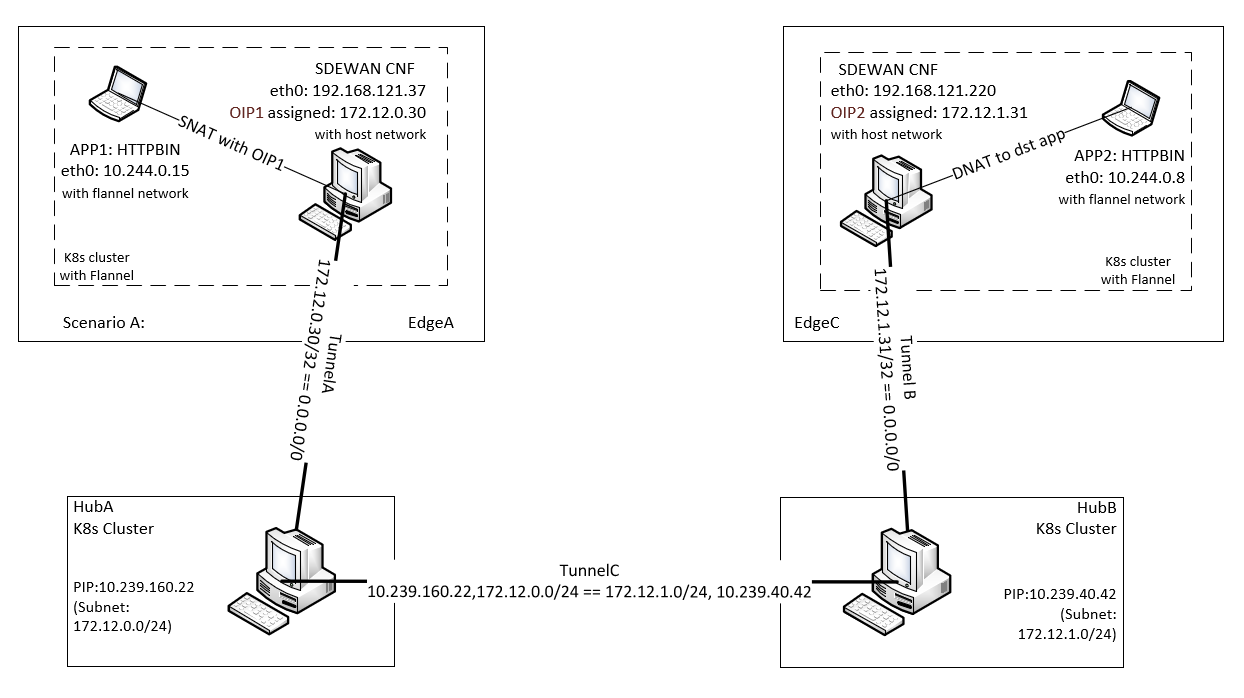
Scenario C: Hub to hub tunnel when inter micro-service communication across edges that attached to different traffic hubs
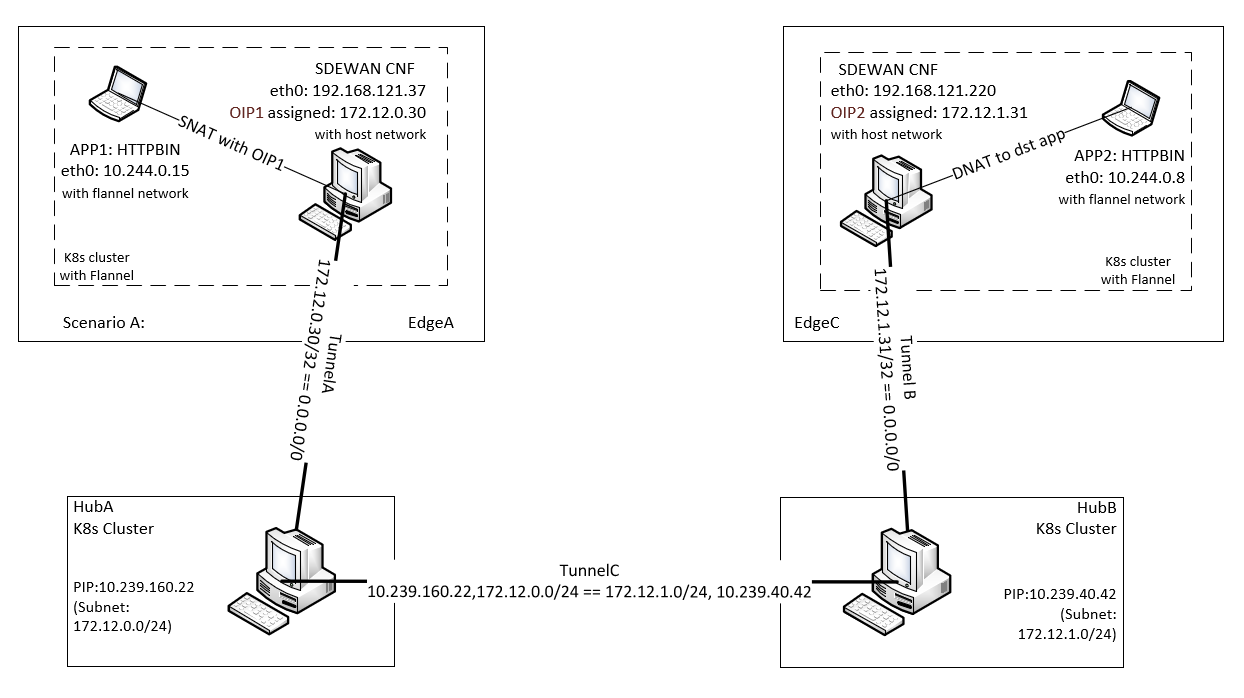 Image Added
Image Added
| Section |
|---|
|
| Column |
|---|
|
| Code Block |
|---|
| language | yml |
|---|
| title | Sample CR for edgeA |
|---|
| collapse | true |
|---|
| CR for sdewan cnf on edgeA:
apiVersion: sdewan.akraino.org/v1alpha1
kind: IpsecHost
metadata:
name: edgeA
namespace: default
labels:
sdewanPurpose: cnf-1
spec:
remote: 10.239.160.22
authentication_method: psk
pre_shared_key: test
crypto_proposal:
- test_proposal_1
connections:
- connection_name: connection_A
type: tunnel
mode: start
local_sourceip: %config
remote_subnet: 0.0.0.0/0, 10.239.160.22/32
crypto_proposal:
- test_proposal_1
status:
appliedVersion: "1"
appliedTime: "2020-04-12T09:28:38Z"
inSync: True |
|
| Column |
|---|
| The CRs defined will then be interpreted into some IPSec configuration that could be recognized by Openwrt and then translate to Strongswan configs |
| Column |
|---|
|
| Code Block |
|---|
| language | yml |
|---|
| title | Strongswan configs for edgeA |
|---|
| collapse | true |
|---|
| Strongswan configs for sdewan cnf on edgeA:
conn edgeB-connection_A
left=%any
right=10.239.160.22
localsourceip=%config
rightsubnet=0.0.0.0/0,10.239.160.22/32
leftauth=psk
rightauth=psk
auto=start
keyexchange=ikev2
ike=aes192-sha1-modp3072
esp=aes192-sha1-modp3072
type=tunnel
|
|
|
| Section |
|---|
|
| Column |
|---|
|
| Code Block |
|---|
| language | yml |
|---|
| title | Sample CR for edgeB |
|---|
| collapse | true |
|---|
| CR for sdewan cnf on edgeB:
apiVersion: sdewan.akraino.org/v1alpha1
kind: IpsecHost
metadata:
name: edgeB
namespace: default
labels:
sdewanPurpose: cnf-1
spec:
remote: 10.239.40.42
authentication_method: psk
pre_shared_key: test
crypto_proposal:
- test_proposal_1
connections:
- connection_name: connection_A
type: tunnel
mode: start
local_sourceip: %config
remote_subnet: 0.0.0.0/0, 10.239.40.42/32
crypto_proposal:
- test_proposal_1
status:
appliedVersion: "1"
appliedTime: "2020-04-12T09:28:38Z"
inSync: True |
|
| Column |
|---|
| The CRs defined will then be interpreted into some IPSec configuration that could be recognized by Openwrt and then translate to Strongswan configs |
| Column |
|---|
|
| Code Block |
|---|
| language | yml |
|---|
| title | Strongswan configs for edgeB |
|---|
| collapse | true |
|---|
| Strongswan configs for sdewan cnf on edgeB:
conn edgeB-connection_A
left=%any
right=10.239.40.42
localsourceip=%config
rightsubnet=0.0.0.0/0,10.239.40.42/32
leftauth=psk
rightauth=psk
auto=start
keyexchange=ikev2
ike=aes192-sha1-modp3072
esp=aes192-sha1-modp3072
type=tunnel
|
|
|
| Section |
|---|
|
| Column |
|---|
|
| Code Block |
|---|
| language | yml |
|---|
| title | Sample CR for HubA |
|---|
| collapse | true |
|---|
| CR on sdewan on hubA:
apiVersion: sdewan.akraino.org/v1alpha1
kind: IpsecSite
metadata:
name: HubA
namespace: default
labels:
sdewanPurpose: cnf-1
spec:
remote: %any
authentication_method: psk
pre_shared_key: test
crypto_proposal:
- test_proposal_1
connections:
- connection_name: connection_A
type: tunnel
mode: start
local_subnet: 172.12.0.1/24,10.239.160.22/32
remote_sourceip: 172.12.0.30-172.12.0.45
crypto_proposal:
- test_proposal_1
status:
appliedVersion: "1"
appliedTime: "2020-04-12T09:28:38Z"
inSync: True
---
apiVersion: sdewan.akraino.org/v1alpha1
kind: IpsecSite
metadata:
name: HubA
namespace: default
labels:
sdewanPurpose: cnf-1
spec:
remote: 10.239.40.42
authentication_method: psk
pre_shared_key: test
crypto_proposal:
- test_proposal_1
connections:
- connection_name: connection_B
type: tunnel
mode: start
local_subnet: 172.12.0.1/24,10.239.160.22/32
remote_subnet: 172.12.1.1/24,10.239.40.42/32
crypto_proposal:
- test_proposal_1
status:
appliedVersion: "1"
appliedTime: "2020-04-12T09:28:38Z"
inSync: True |
|
| Column |
|---|
| The CRs defined will then be interpreted into some IPSec configuration that could be recognized by Openwrt and then translate to Strongswan configs |
| Column |
|---|
|
| Code Block |
|---|
| language | yml |
|---|
| title | Strongswan configs for HubA |
|---|
| collapse | true |
|---|
| Strongswan configs for sdewan cnf on hub:
conn HubA-connection_A
left=%any
leftsubnet=172.12.0.1/24,10.239.160.22/32
rightsourceip=172.12.0.30-172.12.0.45
leftauth=psk
rightauth=psk
auto=start
keyexchange=ikev2
ike=aes192-sha1-modp3072
esp=aes192-sha1-modp3072
type=tunnel
conn HubA-connection_B
left=%any
leftsubnet=172.12.0.1/24,10.239.160.22/32
rightsubnet=172.12.1.1/24,10.239.40.42/32
leftauth=psk
rightauth=psk
auto=start
keyexchange=ikev2
ike=aes192-sha1-modp3072
esp=aes192-sha1-modp3072
type=tunnel
|
|
|
| Section |
|---|
|
| Column |
|---|
|
| Code Block |
|---|
| language | yml |
|---|
| title | Sample CR for HubB |
|---|
| collapse | true |
|---|
| CR on sdewan on hubB:
apiVersion: sdewan.akraino.org/v1alpha1
kind: IpsecSite
metadata:
name: HubB
namespace: default
labels:
sdewanPurpose: cnf-1
spec:
remote: %any
authentication_method: psk
pre_shared_key: test
crypto_proposal:
- test_proposal_1
connections:
- connection_name: connection_A
type: tunnel
mode: start
local_subnet: 172.12.1.1/24,10.239.40.42/32
remote_sourceip: 172.12.1.31-172.12.1.35
crypto_proposal:
- test_proposal_1
status:
appliedVersion: "1"
appliedTime: "2020-04-12T09:28:38Z"
inSync: True
---
apiVersion: sdewan.akraino.org/v1alpha1
kind: IpsecSite
metadata:
name: HubB
namespace: default
labels:
sdewanPurpose: cnf-1
spec:
remote: 10.239.160.22
authentication_method: psk
pre_shared_key: test
crypto_proposal:
- test_proposal_1
connections:
- connection_name: connection_B
type: tunnel
mode: start
remote_subnet: 172.12.0.1/24,10.239.160.22/32
local_subnet: 172.12.1.1/24,10.239.40.42/32
crypto_proposal:
- test_proposal_1
status:
appliedVersion: "1"
appliedTime: "2020-04-12T09:28:38Z"
inSync: True |
|
| Column |
|---|
| The CRs defined will then be interpreted into some IPSec configuration that could be recognized by Openwrt and then translate to Strongswan configs |
| Column |
|---|
|
| Code Block |
|---|
| language | yml |
|---|
| title | Strongswan configs for HubB |
|---|
| collapse | true |
|---|
| Strongswan configs for sdewan cnf on hub:
conn HubB-connection_A
left=%any
leftsubnet=172.12.1.1/24,10.239.40.42/32
rightsourceip=172.12.1.31-172.12.1.35
leftauth=psk
rightauth=psk
auto=start
keyexchange=ikev2
ike=aes192-sha1-modp3072
esp=aes192-sha1-modp3072
type=tunnel
conn HubA-connection_B
left=%any
leftsubnet=172.12.1 |
|
on hub:
apiVersion: sdewan.akraino.org/v1alpha1
kind: IpsecSite
metadata:
name: Hub
namespace: default
labels:
sdewanPurpose: cnf-1
spec:
remote: %any
authentication_method: psk
pre_shared_key: test
crypto_proposal:
- test_proposal_1
connections:
- connection_name: connection_A
type: tunnel
mode: start
local_subnet: 172.12.016022 remote_sourceip: rightsubnet=172.12.0.1/24,10.239.160.42/32
leftauth=psk
rightauth=psk
|
|
crypto_proposal:auto=start
keyexchange=ikev2
|
|
- test_proposal_1
status:
appliedVersion: "1"
appliedTime: "2020-04-12T09:28:38Z"
inSync: True |
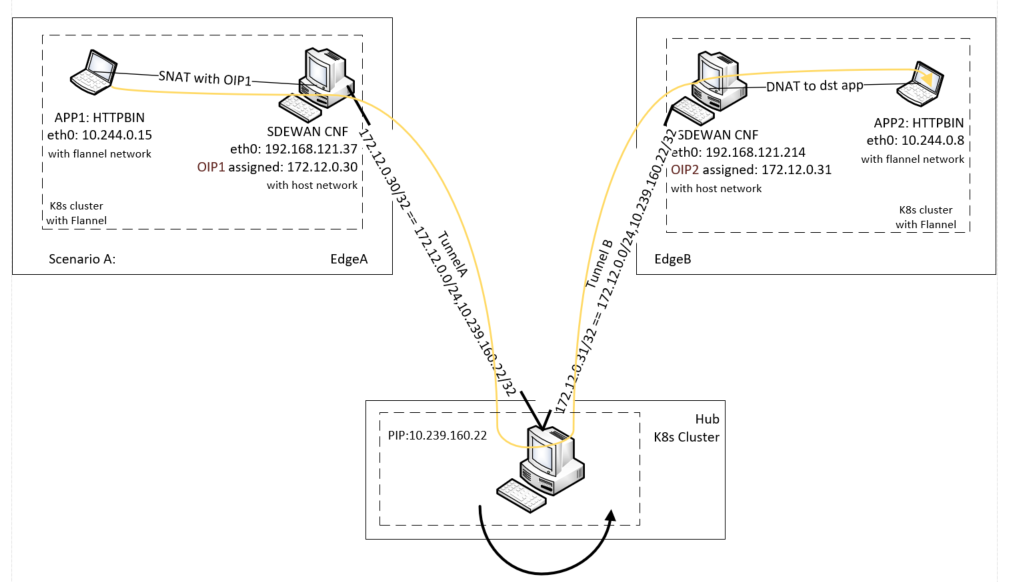
Scenario B: Inter hub secure traffic tunnels
...
ike=aes192-sha1-modp3072
esp=aes192-sha1-modp3072
type=tunnel
|
|
|
Overall scenarios
Here shows the overall scenario we want to achieve in the ICN SDEWAN case.
...