...
Attendance is taken purely upon #info in Zoom Chat (Extended TSC)
| Fujitsu | Ampere Computing | |||
| Alicon | Alibaba Cloud | |||
| Zenlayer | China Unicom | |||
| Signalogic | Coredge.io | |||
| Baidu | PGTalk | |||
| Tencent | Socnoc AI Inc. | |||
| IEEE Future Networks | Arm | |||
沈建发 (Jianfa Shen) proxy by Jiangliu | ByteDance | Salesforce | ||
| China Mobile Research Institute | ||||
| AnyLog | Ysemi Computing |
Time | Agenda Items | Presented By | Presos/Note /Links/ | Meeting Minutes |
|---|---|---|---|---|
| 15 | Akraino Spring Summit Planning | Yin Ding | Planning Committee members: Jim Xu Jeff Brower Wenhui Zhang | |
| 5 | Release 7 Planning | |||
| 10 | PTLs and Subcommittee Chair Update | |||
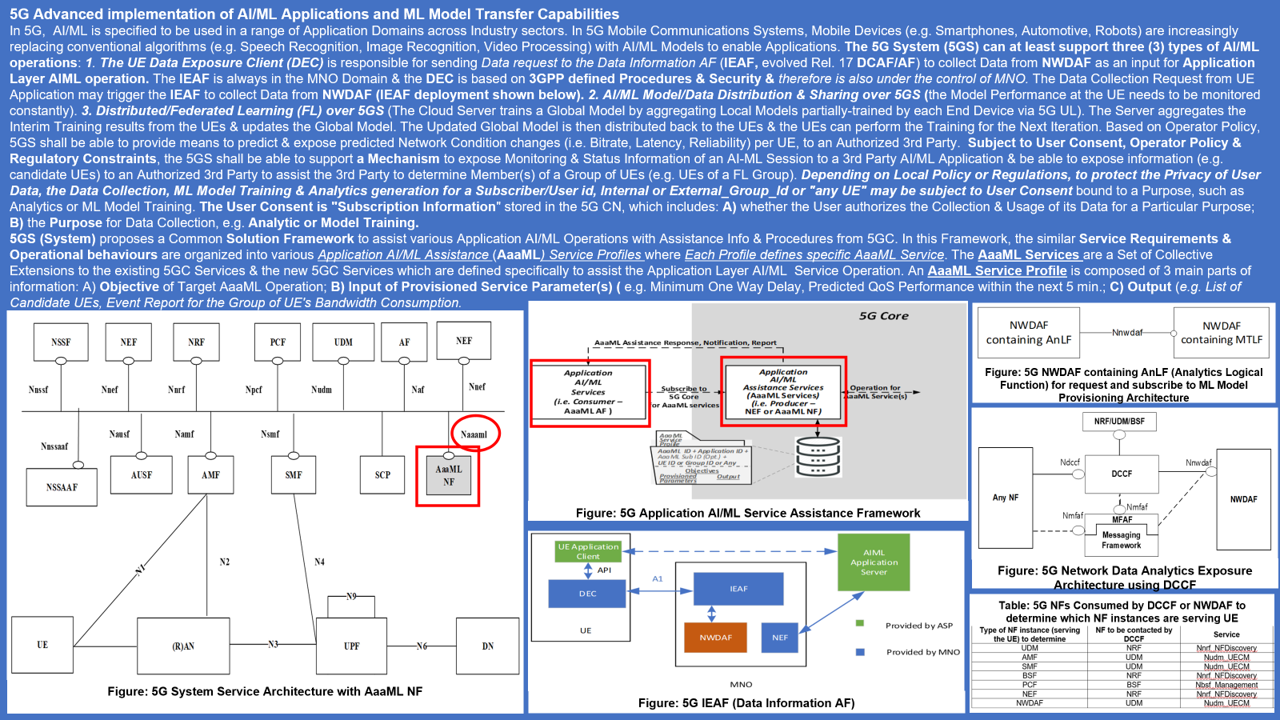
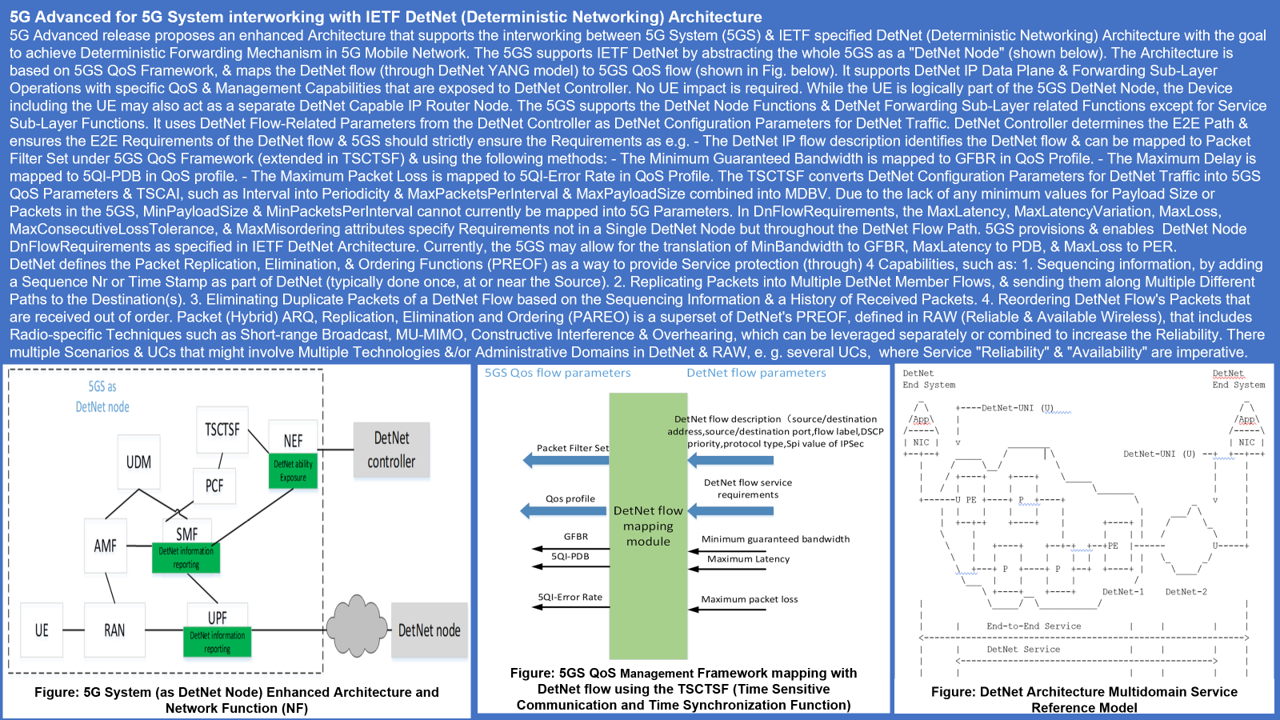
| 10 | Security when using ML | Aspects related to Security when using ML: Brief meeting notes about Ike's diagrams: 1) DetNet is defined in IETF RFC 8398 2) "Subject to User Consent, Operator Policy, and Regulatory Constraints" – this is very broad. I'm not sure what basic assumptions Akraino should use when reviewing and updating its Security policies |
Action Items (Open Action Item Tracker)
...