Table of Contents
Introduction
The guide covers the installation details which are related to Enterprise Applications on Lightweight 5G Telco Edge (EALTEdge) Blueprint.
...
Note: For Development environment two nodes is sufficient, where one node plays a dual role of One-Click Deployment Node and MECM Node with other as MEC Host.
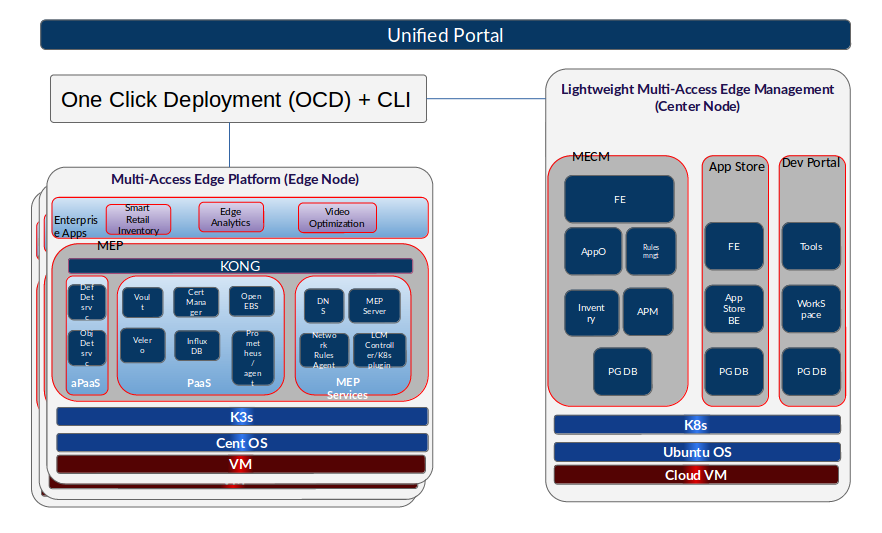
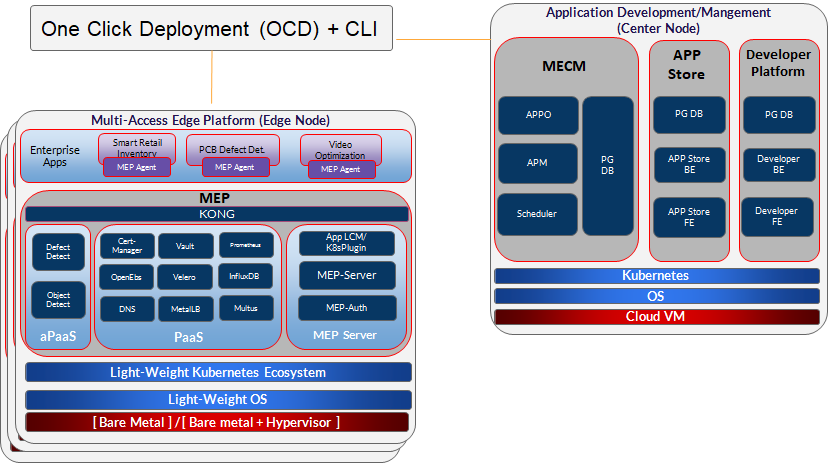
FigureFigure: EALTEdge Deployment Architecture
...
- Install Ansible > 2.9.6 [ https://docs.ansible.com/ansible/latest/installation_guide/intro_installation.html]
- Install git
- Install GoLang > 1.14+
- Git clone the Kubespray repo. [https://github.com/kubernetes-sigs/kubespray.git]
- Install python3 and pip3
- cd kubespray && pip install -r requirements.txt
Jump Host Pre-Configurations for
...
Center Components Installation
...
Login to the Jump Host and perform the below configuration steps (Steps : as below-
...
Update ansible inventory file provided in kubesrpay repo with MECM Cluster node IP's
4. Review and Change Parameters under inventory/mycluster/group_vars
Example:
declare -a IPS=(158.176.15.55 158.176.15.56 158.176.15.57)
CONFIG_FILE=inventory/mycluster/hosts.yaml python3 contrib/inventory_builder/inventory.py ${IPS[@]}
4. Review and Change Parameters under inventory/mycluster/group_vars
cat inventory/mycluster/group_vars/all/all.yml
cat inventory/mycluster/group_vars/k8s-cluster/k8s-cluster.yml
cat inventory/mycluster/group_vars/all/all.yml
cat inventory/mycluster/group_vars/k8s-cluster/k8s-cluster.yml
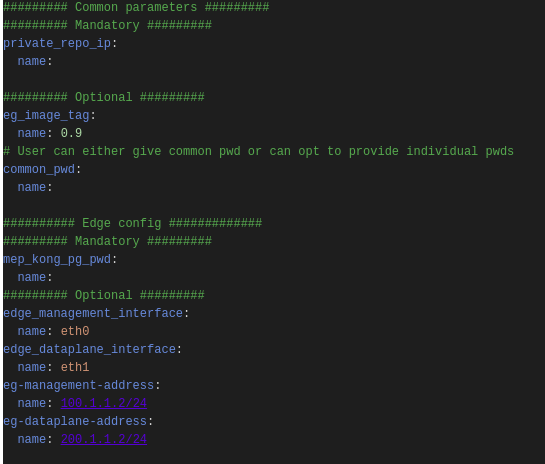
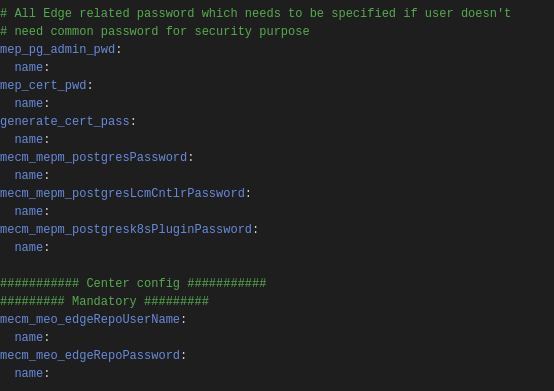
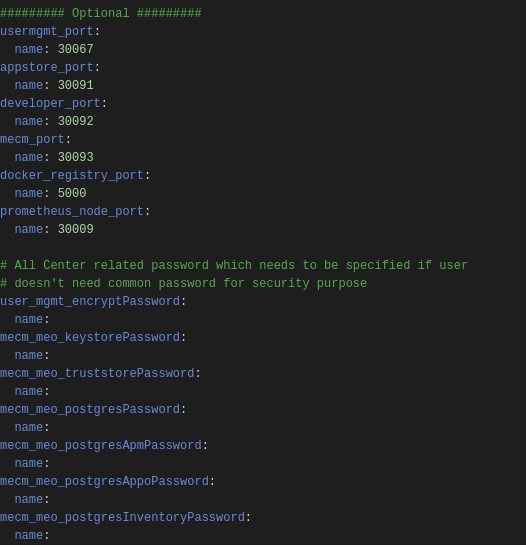
5. 5. Alter the config.yml and change parameters under path NEED TO BE PROVIDEDpath
Installing Mode : EALTEdge using Ansible-Playbooks
...
root@akraino-mec-0002:~#ealt clean all
root@akraino-mec-0002:~#ealt clean edge
Troubleshooting
Error Message Guide
N/A
Maintenance
Blueprint Package Maintenance
Software maintenance
N/A
Hardware maintenance
N/A
Blueprint Deployment Maintenance
N/A
Frequently Asked Questions
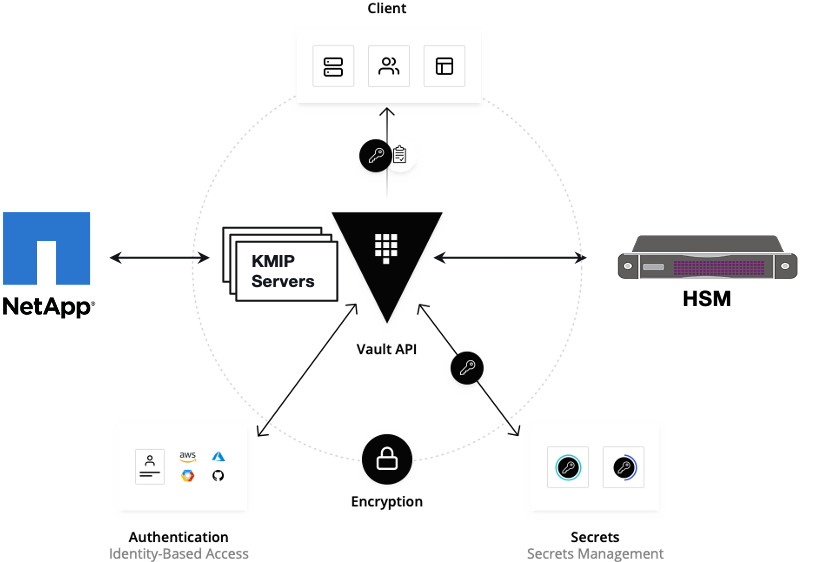
Vault documentation
**This document explains how to generate certificate by using vault and cert manager**
##Cluster Architecture

##Make a cluster
##The Image try to put with reference to our environment, with reference to EALT Edge. Can make a picture where Vault will be running in MEC Host (as Root CA) , ##Cert Manager and Applications (App1, App2)
##1. Add helm repo
```
helm repo add hashicorp https://helm.releases.hashicorp.com
helm install vault hashicorp/vault
```
##2. Generate root token and Unseal Key
```
kubectl exec vault-0 -- vault operator init -key-shares=1 -key-threshold=1 -format=""
```
##Note: Root token we will use when we will login vault pod, Unseal Key and Root token will looks like below ex-
##Unseal Key 1: QcTX47IacKidIjFWSrkGLiQG1fwaqoInEz0SqAZ7rMs=
##Initial Root Token: s.A0SXgscZxbCeJRd1AjsVzvUU
##Generated Unseal key need to put in below command then vault will start running as a pod
```
kubectl exec -ti vault-0 -- vault operator unseal <Unseal Key>
```
##Vault is initialised as a pod
##By using below command can login in vault pod
```
kubectl exec -it vault-0 -- /bin/sh
```
##Vault Initialisation and Configuration Steps
####Once we initialize the vault pod we get unseal key and root token, need to put the root token
```
vault login <root token>
```
##Enable the PKI secrets engine
##By default, the secrets engine will mount at the name of the engine. To enable the secrets engine at a ##different path, use the -path argument.
```
vault secrets enable pki
```
##Keep the value in sync with the comment. 30 days, Increase the TTL by tuning the secrets engine. The default value of 30 days may be too short
```
vault secrets tune -default-lease-ttl=2160h -max-lease-ttl=87600h pki
```
##Configure a CA certificate and private key. It can generate ##its own self-signed root
## ealtedge.com is a your common_name or base url
```
vault write pki/root/generate/internal common_name=ealtedge.com ttl=8760h
```
##Update the CRL location and issuing certificates. These values can be updated in the future.
```
vault write pki/config/urls issuing_certificates="http://127.0.0.1:8200/v1/pki/ca" crl_distribution_points="http://127.0.0.1:8200/v1/pki/crl"
```
##It will allow your domain and subdomain
```
vault write pki/roles/my-role allowed_domains=ealtedge.com allow_subdomains=true max_ttl=8760h
```
##Generate a new credential by writing to the /issue endpoint with the name of the role
##The output will include a dynamically generated private key and certificate which corresponds to the ##given role
##The issuing CA and trust chain is also returned for automation simplicity
```
vault write pki/issue/my-role common_name=www.ealtedge.com
```
####Enabling AppRole in Vault
```
vault auth enable approle
```
##Writing vault policy
```
vault policy write pki-policy -<<EOF
path "pki*" { capabilities = ["create", "read", "update", "delete", "list", "sudo"]}
EOF
```
##Write Auth role
```
vault write auth/approle/role/my-role secret_id_ttl=8760h token_num_uses=0 token_ttl=2160h token_max_ttl=8760h secret_id_num_uses=0 policies=pki-policy
```
##Note:-
##my-role - is the role name
##secret_id_ttl - (Optional) The number of seconds after which any SecretID expires
##token_num_uses - (Optional) The period, if any, in number of seconds to set on the token
##token_ttl - (Optional) The incremental lifetime for generated tokens in number of seconds. Its current value will be referenced at renewal time
##token_max_ttl - (Optional) The maximum lifetime for generated tokens in number of seconds. Its current value will be referenced at renewal time
##secret_id_num_uses - (Optional) The number of times any particular SecretID can be used to fetch a token from this AppRole, after which the SecretID will expire. ##A value of zero will allow unlimited uses.
##Read Auth role
##Here it will give you role id which you need to use in vault-approle-issuer.yml
```
vault read auth/approle/role/my-role/role-id
```
##Generate secret id
```
vault write -f auth/approle/role/my-role/secret-id
```
##By using above 2 command role id and secret id you need to pass in below command
```
vault write auth/approle/login role_id=<role-id> secret_id=<secret-id>
```
###########################
##If the command successful then vault configuration and authentication via approle is completed
###########################
##YAML files to be modified
##First execute below yaml file
```
kubectl apply -f cert-manager.yaml
```
##Need to replace with the latest secret id in base64 format by using below command
##Secret id already generate when we are executing vault command, need to use same secret id here
```
echo secret-id | base64
```
##The output of above command has to be replaced in the vault-apply-secret.yml file data.secretId
```
kubectl apply -f vault-apply-secret.yml
```
##No you will get one ip where your vault is running so that ip you can get by using below command
##Copy vault ip from below command
```
kubectl get svc
```
##Now vault ip and role id need to replace in vault-approle-issuer.yml file
##Role id already generated when we are executing vault commands
```
kubectl apply -f vault-approle-issuer.yml
```
##NOTE: spec.vault.server: IP here you need to change vault ip which you will get when u ren 'kubectl get svc'
##spec.vault.auth.roleId this is you need to replace and need to put latest role id which you get in 'vault read auth/approle/role/my-role/role-id'
##Then final we need to execute below yaml file
```
kubectl apply -f vault-cert-certificate.yml
```
#######################################
Certificate generate process completed
#######################################
##Now get ca certificate use below command
```
curl http://10.43.130.35:8200/v1/pki/ca/pem
```
##10.43.130.35 is your vault ip, need to replace with latest vault ip
Troubleshooting
Error Message Guide
Error: Most of mecm-pods down state including service center pod,
In service center pod logs , "decryption password incorrect" issue
Solution: Please use common_pwd in config.yaml as te9Fmv%qaq
Maintenance
Blueprint Package Maintenance
Software maintenance
N/A
Hardware maintenance
N/A
Blueprint Deployment Maintenance
N/A
Frequently Asked Questions
1) k3s not installed on mec host (edge node) Port 6443
This issue might be due to Port on EDGE node 6443 occupied by some other process. In such case, it will not install k3s and ansible command will fail.
Solution:
We need to release port 6443 and completely uninstall the platform and re-install platform
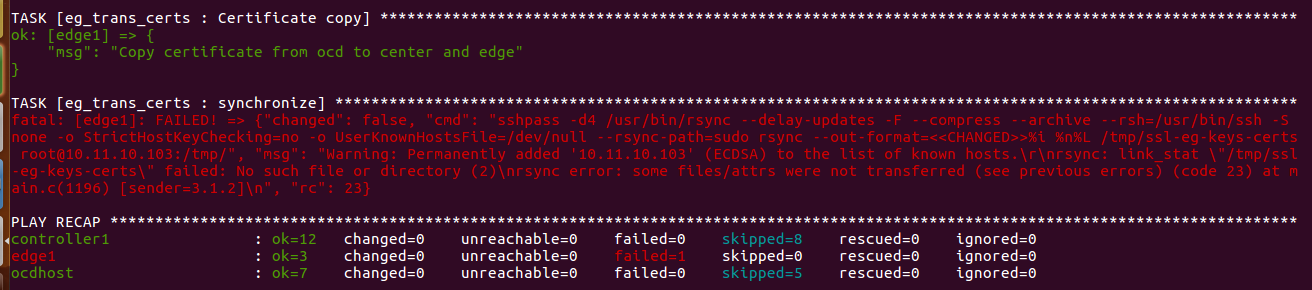
2) eg_trans_certs failure:
The above issue during installation process due to certificate generation again and again continuously without uninstallation process.
Every time our mec edge node installation requires new sets of certs to download and install the Edge gallery related things i.e pods services and so on.
Solution:
So, if once the installation process failed. We ought to completely uninstall and re-install the ealt-edge platform using ansible commands.
Please refer the installation and uninstallation steps provdied above using ansible commands
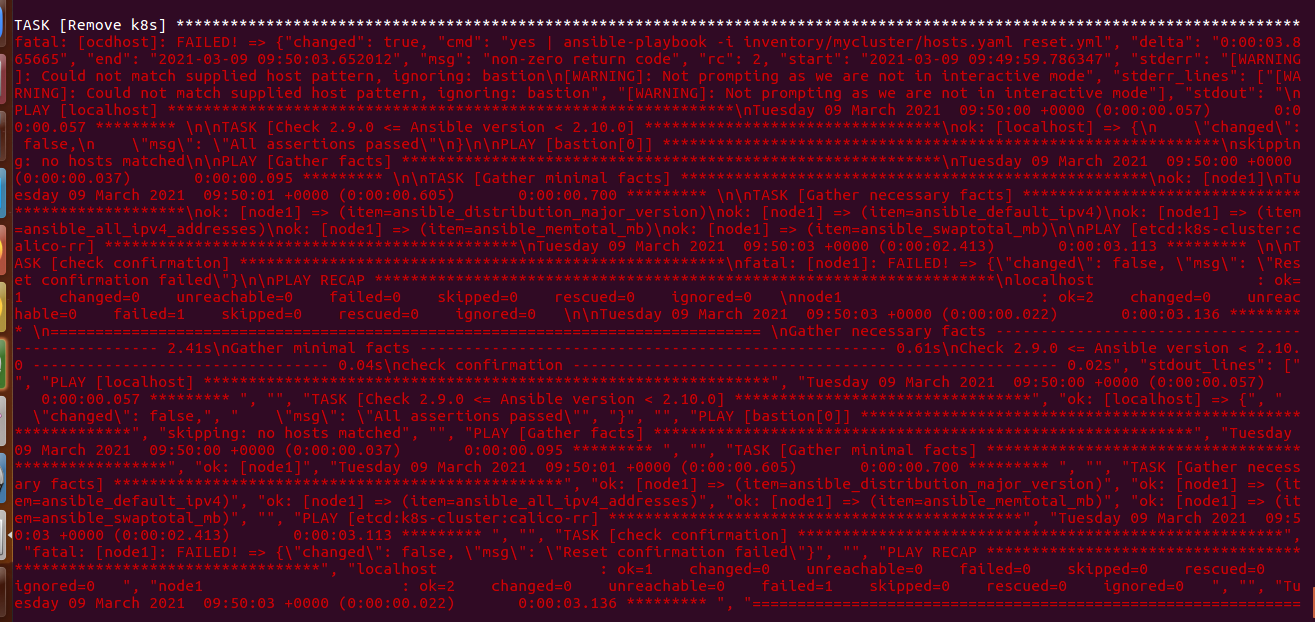
3) K8s remove / uninstallation issue through ansible
If k8s not getting removed or not installed properly or if version changed than our recommended version 1.17.2,
Solution:
In such cases, there might be problem in configuration of kubespray folder and its relevant configurations.
We recommend to configure pre-requisite kubepspray prior to installation process
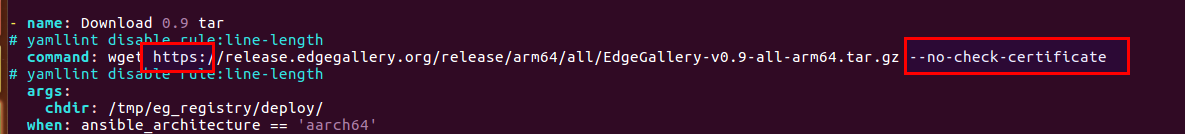
4) eg_registry Download 0.9 tar : issue
If downloading edge gallery 0.9 version tar failed for no reason,
Solution: We can add –no-check-certificate in the wget of Download 0.9 tar in install.yml of eg_registry role. This issue occurs in extremely rare secure environments.
We will be fixing this issue ASAP.
N/A
License
Any software developed by the "Akraino Enterprise Applications on Lightweight 5G Telco Edge Project is licensed under the
Apache License, Version 2.0 (the "License");
you may not use the content of this software bundle except in compliance with the License.
You may obtain a copy of the License at <https://www.apache.org/licenses/LICENSE-2.0>
...
| S. No | Software | Type | Version | License | Remarks |
| 1. | Kubespray | K8S Tool | 2.14.132 | Apache 2.0 license | No code modifications done |
| 2. | Helm | Application Package Manager | 3.0.2 | Apache 2.0 license | No code modifications done |
CENTER Node
Center Node consists of 3 components . MECM , Appstore and Developer Portal.
...
| S. No | Software | Type | Version | License | Remarks |
| 1. | Docker | CRI | 19.03+ | Apache 2.0 license | No code modifications done |
| 2. | Kubernetes | Orchestration | 1 v1. 1917. 32 | Apache 2.0 license | No code modifications done |
| 3. | Helm | Application Package Manager | 3.0.2 | Apache 2.0 license | No code modifications done |
| 4. | Grafana | Monitoring MEC-Graphana | 8- 7. 661. 01 | Apache 2.0 license | Code part of Edge Gallery |
| 5. | Calico | CNI Plugin | 3.16.5 | Apache 2.0 license | No code modifications done |
| 6. | PostgresSQL | MECM-Service | 12.3 | PostgreSQL License | Code part of Edge Gallery |
| 7. | AppLCM | MECM-Service | 0.9 | Apache 2.0 license | Code part of Edge Gallery |
| 8. | Appo | MECM-Service (MECM-Appo) | 0.9 | Apache 2.0 license | Code part of Edge Gallery |
| 9 | Inventory | MECM-Service | 0.9 | Apache 2.0 license | Code part of Edge Gallery |
| 10 | Apm | MECM-Service | 0.9 | Apache 2.0 license | Code part of Edge Gallery |
| 11 | User Management | Part of Center Node | 0.9 | Apache 2.0 license | Code part of Edge Gallery |
| 12 | MECM - FrontEnd | MECM-Service | 0.9 | Apache 2.0 license | Code part of Edge Gallery |
| 13. | Appstore | Service (Part of Center Node) | 0.9 | Apache 2.0 license | Code part of Edge Gallery |
| 14. | Developer Portal | Service (Part of Center Node) | 0.9 | Apache 2.0 license | Code part of Edge Gallery |
| 15 | Service Center | Service (Part of Center Node) | 0.9 | Apache 2.0 license | Code part of Edge Gallery |
...
| S. No | Software | Type | Version | License Information | Remarks |
| 1. | Docker | CRI | 19.03+ | Apache 2.0 license | No code modifications done |
| 2. | K3S | Orchestration | 1.19.4+ | Apache 2.0 license | No code modifications done |
| 3. | Helm | Application Package Manager | 3.0.2 | Apache 2.0 license | No code modifications done |
| 4. | cAdvisor | Container Metrics | v0.36.0 | Apache 2.0 license | No code modifications done |
| 5 | RabbitMQ | Message Broker | 3.7 | Mozilla Public License | No code modifications done. RabbitMQ image is deployed as is. |
| 6 | Prometheus | Metrics Collector | 9.3.1 | Apache 2.0 license | Code part of Edge Gallery |
| 7 | mepm-postgres | Service Database | 9 12. 63 | PostgreSQL License | Code part of Edge Gallery |
| 8 | MEP | Pod | 0.9 | Apache 2.0 license | Code part of Edge Gallery |
| 9 | MECM-MEPM | MEPM-Service | 0.9 | Apache 2.0 license | Code part of Edge Gallery |
...