Goals
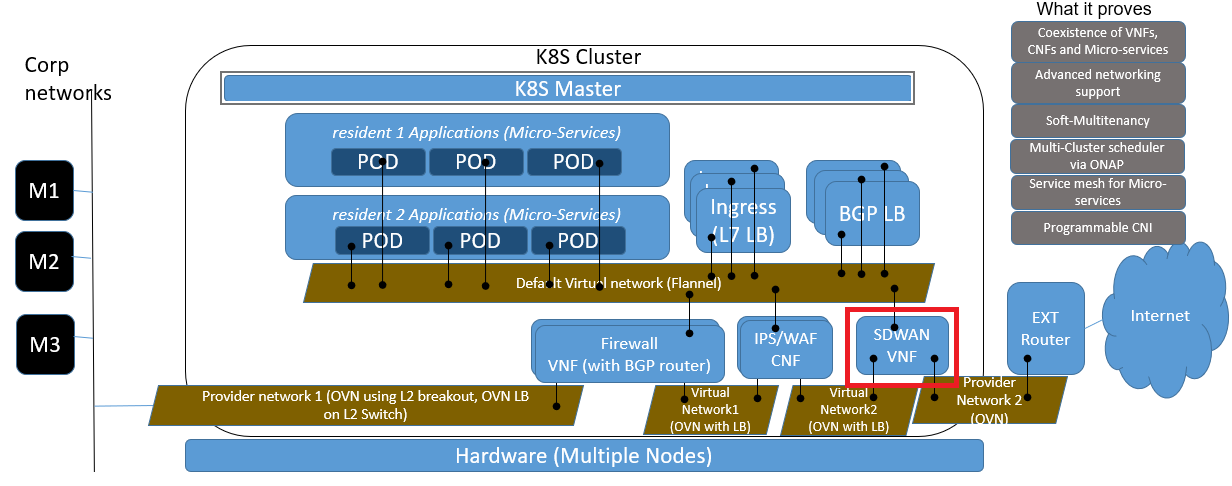
In ICN's SDWAN usages, SFC (Service Function Chain) is designed to support Corp networks to connect to external internet with security connection. The SFC includes Security VNF (e.g. firewall etc.), WAN Opt CNF and SDWAN VNF/CNF, and SDWAN module is worked as software defined router which can be used to defined the rules when connect to external internet. Below diagram shows where SDWAN module located in the whole system.
Basic Technology
OpenWRT
The OpenWRT Project (https://openwrt.org/) is an open source project based on Linux, and it is primarily used on embedded devices to route network traffic. There are more than 3500 software packages which can be installed on OpenWRT via opkg package management system. OpenWRT provides both docker image and VM image to support virtualization solution (https://openwrt.org/docs/guide-user/virtualization/start). In ICN, we run OpenWRT in container.
OpenWRT Mwan3 package (a replacement for multiwan package) provides the capabilities for multiple WAN management: WAN interfaces management, outbound traffic rules, traffic load balancing etc.
ovn4nfv-k8s-plugin
ovn4nfv-k8s-plugin is a CNI plugin based on ovn. It can work together with Multus CNI to add multiple interfaces for the pod. One of the interfaces is the Multus default interface, it could be flannel, calico, etc. The other interfaces are added by ovn4nfv-k8s-plugin according the the pod annotation. With ovn4nfv-k8s-plugin, we can create virtual network in run-time. Also we can connect the pod with the provider network, this is important for CNF.
Design Proposals
Implementation
SDWAN module is implemented as CNF instead of VNF for better performance and proving of CNF can also be effect way to deploy SDWAN
SDWAN will leverage OpenWRT for it functionality:
- Base Image: x86-generic rootfs image (http://downloads.openwrt.org/releases/18.06.4/targets/x86/generic/)
- Packages:
- mwan3: multiple wans configuration and management
- luci-app-mwan3: web configuration interface for mwan3
- uhttp: web server for luci services
Deployment
Helm will be used to deploy SDWAN CNF as pod on nodes with external network connection with below parameters:
- Network interfaces: multiple interfaces from difference CNI plugins, e.g. one is Multus default CNI (e.g. flannel or Calico), one is OVN CNI to connect to virtual network1 then connect to corp network, and the last one is OVN CNI which connect to external router
- WAN configuration: an initial script running in the container will use uci command to do initial WAN configuration based on the input
WAN interface definition (e.g. interface, member etc.)
config interface 'wan' option enabled '1' list track_ip '8.8.4.4' list track_ip '8.8.8.8' list track_ip '208.67.222.222' list track_ip '208.67.220.220' option reliability '2' option count '1' option timeout '2' option interval '5' option down '3' option up '8'
config member 'wan_m1_w3' option interface 'wan' option metric '1' option weight '3'
Initial Traffic rules (e.g. policy, rule etc.)
config policy 'wan_only' list use_member 'wan_m1_w3'
config rule 'sticky_even' option src_ip '0.0.0.0/0.0.0.1' option dest_port '443' option proto 'tcp' option use_policy 'wan_only'
Runtime Configuration
SDWAN traffic rules and WAN interfaces are required to be configured at runtime through Restful API interface.
OpenWRT luci invoking mechanism:
(1) logon: POST /cgi-bin/luci with luci_username and luci_password to get sysauth Cookie
e.g. wget --post-data "luci_username=root&luci_password=" http://192.168.56.2/cgi-bin/luci/
response header will include sysauch cookie, like: "Set-Cookie: sysauth=e5b2e5c2ae0099c078bb3cb72052ed95;"
(2) Call luci http service with sysauth Cookie
e.g. wget --header="Cookie:sysauth=e5b2e5c2ae0099c078bb3cb72052ed95" http://192.168.56.2/cgi-bin/luci
Mwan3 supported services:
interface_status: GET /cgi-bin/luci/admin/status/mwan/interface_status
Sample response:
"interfaces":{"wan":{"running":true,"score":0,"track_ip":[{"status":"down","latency":0,"packetloss":0,"ip":"208.67.220.220"},{"status":"down","latency":0,"packetloss":0,"ip":"208.67.222.222"},{"status":"down","latency":0,"packetloss":0,"ip":"8.8.4.4"},{"status":"down","latency":0,"packetloss":0,"ip":"8.8.8.8"}],"lost":536,"status":"offline","age":5,"turn":134},"wanb6":{"running":false,"score":0,"track_ip":[],"lost":0,"status":"","age":0,"turn":0},"wanb":{"running":false,"score":0,"track_ip":[],"lost":0,"status":"","age":0,"turn":0},"wan6":{"running":false,"score":0,"track_ip":[],"lost":0,"status":"","age":0,"turn":0}},"connected":{"ipv6":["Members:","fe80::\/64"],"ipv4":["Members:","224.0.0.0\/3","192.168.56.2","127.0.0.0\/8","127.255.255.255","192.168.56.0\/24","10.0.3.0\/24","10.0.3.15","127.0.0.0","192.168.56.255","127.0.0.1","192.168.56.0","10.0.3.0","10.0.3.255"]}
- detaild_status: GET /cgi-bin/luci/admin/status/mwan/detailed_status
- diagnostics_display: GET /cgi-bin/luci/admin/status/mwan/diagnostics_display
- troubleshooting_display: GET /cgi-bin/luci/admin/status/mwan/troubleshooting_display
Note: configuration for WAN's interface, member, policy and rule are supported in the web UI, but with no direct restful API available. It needs implement luci cgi plugin to provide restful API for WAN configuration. In ICN, one interface is implemented as POC to support running commands in CNF through Rest API call.
command:
POST /cgi-bin/luci/admin/config/command
Execute commands in OpenWRT CNF
Normal Response Code: 200
Error Response Code: 400
Request:
Name In Type Description command Body String commands to be executed in CNF, each command is separated by semicolon
SDWAN CNF Controller Implementations
The Akraino-SDEWAN-OutOfBoxNetworking.pptx describes the whole SDEWAN solution design.
ICN R3 release will focus on implementing the SDEWAN CNF and EWAN config Agent then designing the End-to-End demo with other components described in the SDEWAN solution.
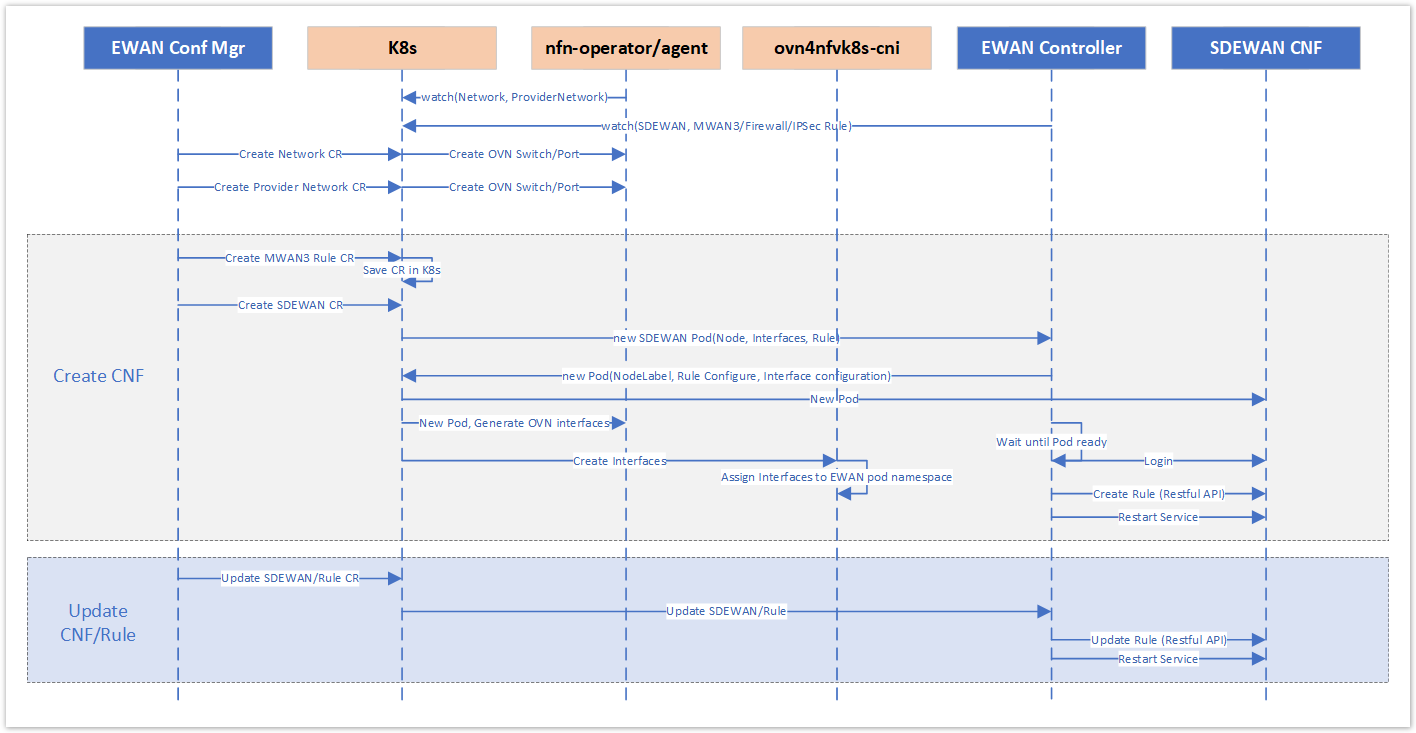
Below diagram describes the interaction between SDEWAN CNF and EWAN config Agent.
Timeline
| Module | Tasks | Owner | Due | Current Status | Description |
|---|---|---|---|---|---|
| PORs | |||||
| POC | Setup IPSec tunnel | Ruoyu | Feb.26 | WW09: setup POC environment by manual configuration (Site-2-Site, Initiator-responder, Initiator-responder with vip) - Done | |
| SDEWAN CNF | |||||
| Service API | Huifeng | Done | Start/stop/restart/reload SDWAN service, includes: mwan3, firewall/NAT, IpSec. Reference: SDEWAN CNF#SDEWANService | ||
| MWAN3 API | Huifeng | Done | Support MWAN3 rule/policy configuration. Reference: SDEWAN CNF#MWAN3 OpenWRT Reference: https://openwrt.org/docs/guide-user/network/wan/multiwan/mwan3 | ||
| Firewall API | Huifeng | Design: Feb.26 Implementation: Mar.12 | WW08: Initial design Done WW09: Implementation - 50% WW10: 80% WW11: implementation | Support firewall configuration for zone (general rule for a group of interfaces), forwarding (iptables forward), rule, redirect (DNAT/SNAT). Reference: SDEWAN CNF#Firewall OpenWRT Reference: https://openwrt.org/docs/guide-user/firewall/firewall_configuration | |
| IPSec API | Ruoyu | Design: Feb.26 Implementation: Mar.18 | WW08: Initial design Done WW09: design done (to be reviewed) WW10: 30% done WW11: implementation | Support IPSec configuration for remote site, proposal. Reference: https://wiki.akraino.org/display/AK/IPSec+Design#IPSecDesign-IPSecRestAPI OpenWRT Reference: https://openwrt.org/docs/guide-user/services/vpn/ipsec/strongswan/start (Note: OpenWRT Wiki page is out-of-date compare to 18.06 implementation which we used and the current design is based on openwrt ipsec code directly) | |
| SDEWAN CNF Controller | |||||
| SDEWAN CRD | Cheng | Done | Define a SDWAN CNF with mwan3, firewall and IPSec configuration Reference: Sdewan config Agent | ||
| MWAN3 CRD | Cheng | Design: Done Implementation: Feb. 26 | WW08: CRD design done, implementation: - Done | Define MWAN3 configuration (policy, rule) Reference: Sdewan config Agent | |
| Firewall CRD | Cheng | Design: Feb.26 Implementation: Mar.12 | WW09: CRD design - Done WW10/11: Implementation | Define Firewall CRD (zone, forwarding, rule, redirect (NAT)) | |
| IPSec CRD | Ruoyu | Design: Feb.26 Implementation: Mar.18 | WW08: initial design done WW09: design done (to be reviewed) WW10/11: Implementation | Define IPSec CRD (remote site, proposal) Reference: https://wiki.akraino.org/display/AK/IPSec+Design#IPSecDesign-IPSecCRD Scenario design: SD-EWAN Scenarios | |
| Integration | CNF controller and CNF Rest API integration | ||||
| MWAN3 | Cheng/Huifeng | Feb.26 | WW09: integration - Done | MWAN3 CRD/Restful API integration | |
| Firewall | Cheng/Huifeng | Mar.26 | Firewall CRD/Restful API integration | ||
| IPSec | Ruoyu/Huifeng | Apr.1 | IPSec CRD/Restful API integration | ||
| SDEWAN demo | E2E demo for SDEWAN solution | ||||
| Demo scenario design | All | Apr.8 | Design E2E demo scenario and setup the environment | ||
| Demo scenario integration | All | Apr.15 | E2E working flow enabling | ||
| Stretch Goals | |||||
| SDWAN Hub Controller | EWAN Config Manager: call EWAN Conf Agent to configure EWAN CNF | Rama | |||
| Key | Store key in TPM | Cheng | |||
| QAT Support | Investigate how to enable QAT support for IPSec (Client library such as OpenSSL configuration, kernel module is not need in CNF) | Ruoyu |
SDEWAN CNF
Sdewan config Agent
Presentation
ICN Weekly meeting video recordings- Weekly Akraino ICN Engineering Meeting