...
| CVE-ID | CVSS | NVD | Fix/Notes |
|---|---|---|---|
| CVE-2016-1585 | 9.8 | https://nvd.nist.gov/vuln/detail/CVE-2016-1585 | No fix available |
| CVE-2021-20236 | 9.8 | https://nvd.nist.gov/vuln/detail/CVE-2021-20236 | No fix available (latest release of ZeroMQ for Ubuntu 20.04 is 4.3.2-2ubuntu1) |
| CVE-2021-31870 | 9.8 | https://nvd.nist.gov/vuln/detail/CVE-2021-31870 | No fix available (latest release of klibc for Ubuntu 20.04 is 2.0.7-1ubuntu5) |
| CVE-2021-31872 | 9.8 | https://nvd.nist.gov/vuln/detail/CVE-2021-31872 | No fix available (latest release of klibc for Ubuntu 20.04 is 2.0.7-1ubuntu5) |
| CVE-2021-31873 | 9.8 | https://nvd.nist.gov/vuln/detail/CVE-2021-31873 | No fix available (latest release of klibc for Ubuntu 20.04 is 2.0.7-1ubuntu5) |
| CVE-2021-33574 | 9.8 | https://nvd.nist.gov/vuln/detail/CVE-2021-33574 | Will not be fixed in Ubuntu stable releases |
| CVE-2021-45951 | 9.8 | https://nvd.nist.gov/vuln/detail/CVE-2021-45951 | No fix available (vendor disputed) |
| CVE-2021-45952 | 9.8 | https://nvd.nist.gov/vuln/detail/CVE-2021-45952 | No fix available (vendor disputed) |
| CVE-2021-45953 | 9.8 | https://nvd.nist.gov/vuln/detail/CVE-2021-45953 | No fix available (vendor disputed) |
| CVE-2021-45954 | 9.8 | https://nvd.nist.gov/vuln/detail/CVE-2021-45954 | No fix available (vendor disputed) |
| CVE-2021-45955 | 9.8 | https://nvd.nist.gov/vuln/detail/CVE-2021-45955 | No fix available (vendor disputed) |
| CVE-2021-45956 | 9.8 | https://nvd.nist.gov/vuln/detail/CVE-2021-45956 | No fix available (vendor disputed) |
| CVE-2021-45957 | 9.8 | https://nvd.nist.gov/vuln/detail/CVE-2021-45957 | No fix available (vendor disputed) |
| CVE-2022-23218 | 9.8 | https://nvd.nist.gov/vuln/detail/CVE-2022-23218 | Reported fixed in 2.31-0ubuntu9.7 (installed), but still reported by Vuls |
| CVE-2022-23219 | 9.8 | https://nvd.nist.gov/vuln/detail/CVE-2022-23219 | Reported fixed in 2.31-0ubuntu9.7 (installed), but still reported by Vuls |
| CVE-2016-9180 | 9.1 | https://nvd.nist.gov/vuln/detail/CVE-2016-9180 | No fix available |
| CVE-2021-35942 | 9.1 | https://nvd.nist.gov/vuln/detail/CVE-2021-35942 | Reported fixed in 2.31-0ubuntu9.7 (installed), but still reported by Vuls |
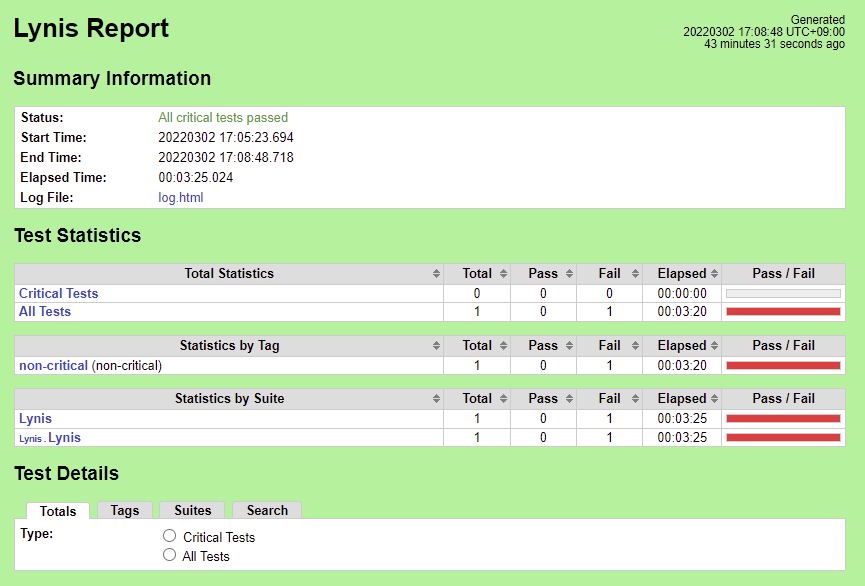
Lynis
The initial results compare with the Lynis Incubation: PASS/FAIL Criteria, v1.0 as follows.
The Lynis Program Update test MUST pass with no errors.
2022-03-04 15:33:28 Test: Checking for program update...
2022-03-04 15:33:31 Current installed version : 301
2022-03-04 15:33:31 Latest stable version : 307
2022-03-04 15:33:31 Minimum required version : 297
2022-03-04 15:33:31 Result: newer Lynis release available!
2022-03-04 15:33:31 Suggestion: Version of Lynis outdated, consider upgrading to the latest version [test:LYNIS] [details:-] [solution:-]
Fix: Download and run the latest Lynis directly on SUT.
The following list of tests MUST complete as passing
| No. | Test | Result | Fix |
|---|---|---|---|
| 1 | Test: Checking PASS_MAX_DAYS option in /etc/login.defs | Result: password minimum age is not configured Suggestion: Configure minimum password age in /etc/login.defs [test:AUTH-9286] | |
| 2 | Performing test ID AUTH-9328 (Default umask values) | Result: found umask 022, which could be improved Suggestion: Default umask in /etc/login.defs could be more strict like 027 [test:AUTH-9328] | |
| 3 | Performing test ID SSH-7440 (Check OpenSSH option: AllowUsers and AllowGroups) | Result: SSH has no specific user or group limitation. Most likely all valid users can SSH to this machine. Hardening: assigned partial number of hardening points (0 of 1). | |
| 4 | Test: checking for file /etc/network/if-up.d/ntpdate | Test: checking for file /etc/network/if-up.d/ntpdate Result: file /etc/network/if-up.d/ntpdate does not exist ... Hardening: assigned maximum number of hardening points for this item (3). | OK |
| 5 | Performing test ID KRNL-6000 (Check sysctl key pairs in scan profile) : Following sub-tests required | N/A | N/A |
| 5a | sysctl key fs.suid_dumpable contains equal expected and current value (0) | Result: sysctl key fs.suid_dumpable has a different value than expected in scan profile. Expected=0, Real=2 | |
| 5b | sysctl key kernel.dmesg_restrict contains equal expected and current value (1) | Result: sysctl key kernel.dmesg_restrict has a different value than expected in scan profile. Expected=1, Real=0 | |
| 5c | sysctl key net.ipv4.conf.default.accept_source_route contains equal expected and current value (0) | Result: key net.inet.ip.sourceroute does not exist on this machine ... Hardening: assigned maximum number of hardening points for this item (1) | OK |
| 6 | Test: Check if one or more compilers can be found on the system | Result: found installed compiler. See top of logfile which compilers have been found or use /usr/bin/grep to filter on 'compiler' Hardening: assigned partial number of hardening points (1 of 3). |
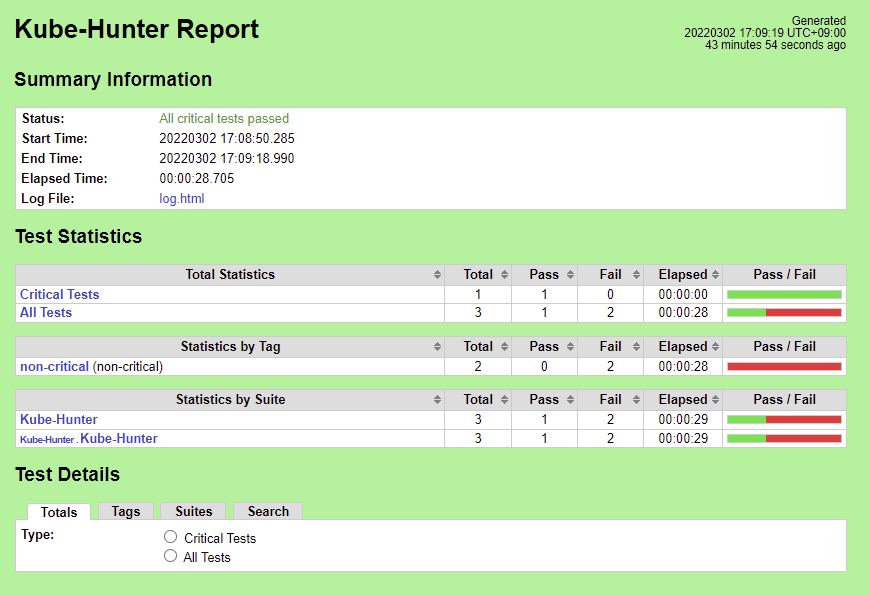
Kube-Hunter
There are 5 Vulnerabilities.
...