Introduction
This document outlines the steps to deploy Radio Edge Cloud (REC). REC was designed from the ground up to be a highly available, flexible, and cost-efficient system for the use and support of Cloud RAN and 5G networks.
Pre-Installation Requirements for REC Cluster
Hardware Requirements:
REC is a fully integrated stack from the hardware up to and including the application, so for best results it is necessary to use one of the tested hardware configurations. Although REC is intended to run on a variety of different hardware platforms, it includes a hardware detector component that customizes each installation based on the hardware present and will need (possibly minor) changes to run on additional hardware configurations. Preliminary support is present in Akraino Release 1 of REC for HP DL380 generation 9 and 10, Dell R740xd and Nokia Open Edge servers, but the primary focus of Release 1 testing is the Nokia Open Edge servers, so some issues may be encountered with other server types.
- Minimum of 3 nodes.
- Total Physical Compute Cores: 60 (120 vCPUs)
- Total Physical Compute Memory: 192GB minimum per node
- Total SSD-based OS Storage: 2.8 TB (6 x 480GB SSDs)
- Total Application-based Raw Storage: 5.7 TB (6 x 960GB SSD0
- Networking Per Server: Apps - 2 x 25GbE (per Server) and DCIM - 2 x 10GbE + 1 1Gbt (shared)
The specific recommended configuration as of the Release 1 timeframe is the Open Edge configuration documented in the Radio Edge Cloud Validation Lab
BIOS Requirements:
- BIOS set to Legacy (Not UEFI)
- CPU Configuration/Turbo Mode Disabled
- Virtualization Enabled
- IPMI Enabled
- Boot Order set with Hard Disk listed as first in list.
Network Requirements:
The REC cluster requires the following segmented (VLAN), routed networks accessible by all nodes in the cluster:
- External Operations, Administration and Management (OAM) Network
- Out Of Band (OOB) (iLO/iDRAC) network(s)
- Storage/Ceph network(s)
- Internal network for Kubernetes connectivity
- NTP and DNS accessibility
The REC installer will configure NTP and DNS using the parameters entered in the user_config.yaml. However, the network
must be configured for the REC cluster to be able to access the NTP and DNS servers prior to the install.
User_config.yaml
The user_config.yaml file contains details for your REC cluster such as required network CIDRs, usernames, passwords,
DNS and NTP server ip addresses, etc. The REC configuration is flexible, but there are dependencies: e.g. using dpdk
requires networking profile with ovs-dpdk type, performance profile with CPU pinning & hugepages and performance
profile link on compute node
The following link points to the latest user_config template with descriptions and examples for every available parameter:
*Note: the version number listed in the user_config.yaml needs to follow closely the version from the template. There is a strict version checking during deployment for the first two part of the version number. The following rules apply to the yaml's version parameter:
### Version numbering: ### X.0.0 ### - Major structural changes compared to the previous version. ### - Requires all users to update their user configuration to ### the new template ### a.X.0 ### - Significant changes in the template within current structure ### (e.g. new mandatory attributes) ### - Requires all users to update their user configuration according ### to the new template (e.g. add new mandatory attributes) ### a.b.X ### - Minor changes in template (e.g. new optional attributes or ### changes in possible values, value ranges or default values) ### - Backwards compatible
YAML Requirements
- The YAML files need to edited/created using Linux editors or in Windows Notepad++
- YAML files do not support TABS. You must space over to the location for the text.
Note: You have better chance at creating a working YAML by editing an existing file or using the template rather then starting from scratch.
Installing REC
Obtaining the ISO Image
Recent builds can be obtained from the Akraino Nexus server. Choose either "latest" or a specific build number from the release images directory and download the file rec.iso. Options for booting the ISO on your target hardware include NFS, HTTP or USB memory stick. You must place the ISO in a suitable location (e.g. NFS server, HTTP(S) server or USB memory stick prior to starting the boot process.
Accessing REC.ISO
Nokia OpenEdge Servers
Login to the controller-1 BMC ip.
Go to Settings/Media Redirection/General Settings.
Select the Remote Media Support.
Select the Mount CD/DVD.
Type the NFS server IP address.
Type the NFS share path.
Select the nfs in Share Type for CD/DVD.
Click Save.
Click OK to restart the VMedia Service.
Go to Settings/Media Redirection/Remote Images.
Select the image for the first CD/DVD device from the drop-down list.
Click the play button to map the image with the server’s CD/DVD devices. The Redirection Status changes to Started when the image redirection succeeds.
Go to Control & Maintain/Remote Control to open the Remote Console.
Reset the server.
Press F7 to boot menu and select boot from CD/DVD device.
HP Servers
Login to iLo for Controller 1 for the installation
Go to Remote Console & Media
Scroll to HTML 5 Console
- URL
http://XXX.XXX.XXX.XX:XXXX/REC_RC1/rec.iso -> Virtual Media URL →
- NFS
< IP to connect for NFS file system>/<file path>/rec.iso
Check “Boot on Next Reset” -> Insert Media
Reset System
Dell Servers
Go to Configuration/Virtual Media
Scroll down to Remote File Share and enter the url for ISO into the Image File Path field.
- URL:
http://XXX.XXX.XXX.XX:XXXX/REC_RC1/rec.iso
- NFS
< IP to connect for NFS file system>/<file path>/rec.iso>
Select Connect.
Open Virtual Console, and go to Boot
Set Boot Action to Virtual CD/DVS/ISO
Then Power/Reset System
After rebooting, the installation will bring up the Akraino Edge Stack screen.
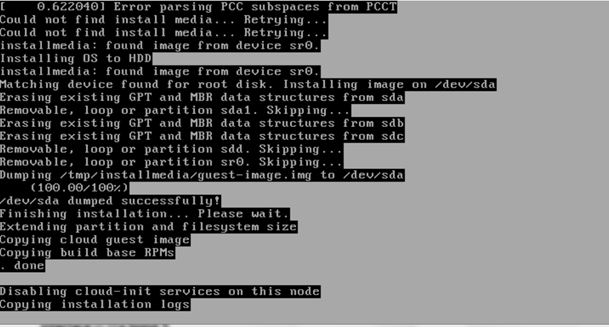
The first step is to clean all the drives discovered before installing the ISO image.
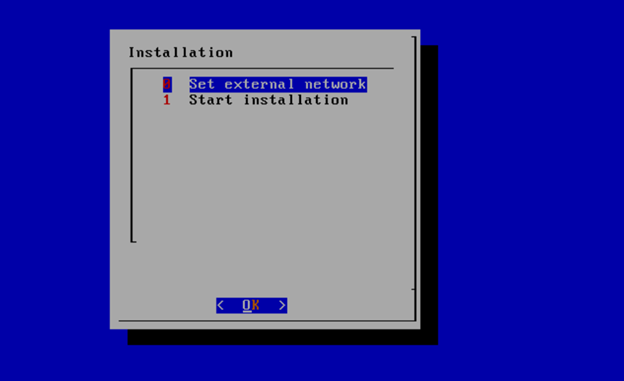
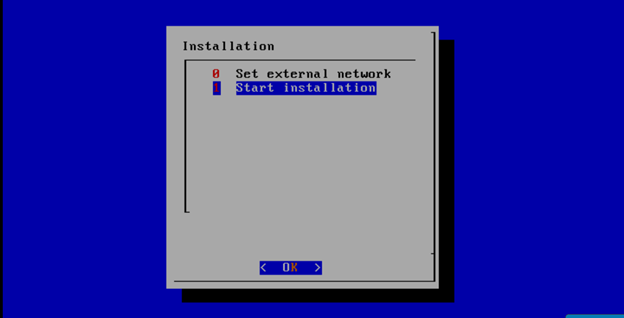
Select, 0 Set external network at the Installation window, press OK.
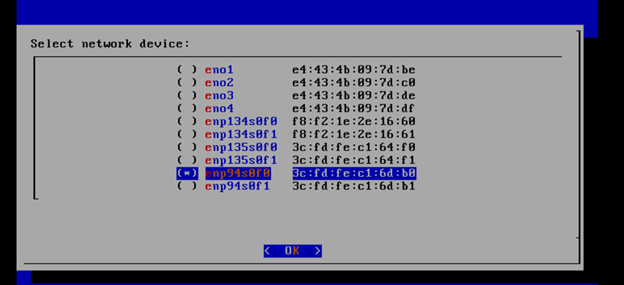
Arrow down to and press the spacebar to select the network interface to be used for the external network.
If using bonded nics, select the first interface in the bond.
Enter the external ip address with CIDR for controller-1: 172.28.15.211/24
Enter the gateway ip address for the external ip address just entered: 172.28.15.1
Enter the VLAN number: 141
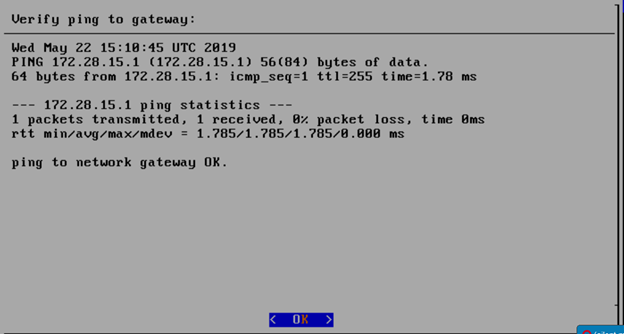
The installation will check the link and connectivity of the IP addresses entered.
If connectivity test passed, then Installation window will return.
Uploading user_config.yaml
Go to your RC or jump server and scp (or sftp) your user_config.yaml to controller-1’s /etc/userconfig directory.
initial credentials: root/root.
scp user_config.yaml root@<controller-1 ip address>/etc/userconfig/
Select, 1 Start installation and OK.
After selecting Start Installation, the installation should start automatically and the content of /srv/deployment/log/bootstrap.log should be displayed on the remote console.
Monitoring Deployment Progress/Status
You can monitor the REC deployment by checking the remote console screen or by tailing the logs on controller-1 node's /srv/deployment/log/ directory.
There are two log files:
bootstrap.log
cm.log
tail -f /srv/deployment/log/cm.log
tail -f /srv/deployment/log/bootstrap.log
Note: When the deployment to all the nodes has completed, “controller-1” will reboot automatically.
Verifying Deployment
A post installation verification is required to ensure that all nodes and services were properly deployed.
You need to establish an ssh connection to the controller’s VIP address and login with administrative rights.
tail /srv/deployment/log/bootstrap.log
You should see: Installation complete, Installation Succeeded.
Go to REC Test Document and follow the steps outlined there to ensure that all nodes and services were properly deployed.
Deployment Failures
Sometimes failures happen, usually do to misconfigurations or incorrect addresses entered.
To re-launch a failed deployment
There are two options for redeploying.(Execute as root)
- /opt/cmframework/scripts/bootstrap.sh --install /etc/userconfig/user_config.yaml &
- openvt -s -w /opt/start-menu/start_menu.sh &
Note: In some cases modifications to the user_config.yaml may be necessary to resolve a failure.
If re-deployment is not possible, then the deployment will need to be started from booting to the REC.iso,